Core Innovation Highlights
Intelligence-driven active defense system
traditionalData SecurityProtection has long relied on a reactive architecture of ”blacklists + rule engines”, whose fundamental flaw is that protection always lags behind the evolution of threats.The first domestic data security intelligent bodyAdopting a reasoning engine based on a large language model, the system is endowed with a complete intelligent closed loop of "perception-cognition-decision-response". The system not only recognizes known attack characteristics, but more importantly, through deep learning and reinforcement learning mechanisms, it makes probabilistic predictions and adaptive protection against unknown threats. This intelligence-driven paradigm enables security protection to evolve from "passive catch-up" to "active prediction", significantly improving the timeliness and accuracy of threat discovery.
The system's built-in AI analytics engine is capable of detecting anomalous data access behavior with millisecond latency. By building a massive data generalization model, the system has been able to identify sensitive data types of more than 99% in the enterprise environment and monitor their flow process in real time. The realization of this capability is based on deep semantic understanding of enterprise data and learning of behavioral patterns, which improves the accuracy rate by 5-10 times compared to the traditional regular expression-based detection method.
Zero Trust ArchitectureThe fine-grained permission model under
In cloud-native and hybrid cloud production environments, traditional boundary protection has become completely ineffective. The first domesticData Securityintelligent bodyon the basis ofzero-trust securityThe system adopts the ”least privilege” principle to ensure that users can only access the smallest set of data within their job responsibilities at any time. The system adopts a dynamic permission allocation mechanism based on the principle of "least privilege" to ensure that users can only access the smallest set of data within the scope of their job responsibilities at any given moment.
The innovation of this architecture is the introduction of AI-driven Contextual Awareness engine, which enables the system to dynamically adjust the permission policy based on multiple factors, such as access time, geographic location, access device, and access mode, to prevent the utilization of abnormal access modes. When detecting privilege oversteps or abnormal login behavior, the system can make isolation decisions within a sub-second delay, realizing a truly three-dimensional zero-trust defense of "identity minimization, privilege minimization, and network minimization".
Technological Innovations in Privacy Computing and Data Immobilization
In the era of proliferation of AI applications, how to both protect data privacy and give full play to the value of data has become the core dilemma faced by enterprises. The first domesticData Security IntelligenceA fusion solution of multiple privacy computing technologies is used, includingCredible implementation environment(TEE),differential privacy(Differential Privacy), Secure Multi-Party Computation (SMC), and others.
The system does this by executing in a trusted hardware environmentAI modelThe reasoning ensures that sensitive data is always encrypted during the computation process, realizing the end-cloud cooperative model of ”computation without breaking confidentiality”. The differential privacy mechanism prevents the model from overfitting a single data record by injecting carefully calibrated noise into the gradient update process, thus avoiding accidental disclosure of private information in the training data during inference. This combination of techniques ensures that even if an attacker gains access to the entire model, he or she is unable to counter-perform the original sensitive data.
Automated operational capabilities with multi-intelligence collaboration
traditionalSafe operationCenter (SOC) is facing the biggest challenge: a serious shortage of expert analysts and a serious lag in the disposal efficiency of attacks. China's first data security intelligence realizes complete automation of threat detection, traceability analysis, impact assessment, and response decision-making through a multi-intelligence collaborative architecture.
The system contains at least five types of specialized intelligences within it, each with different responsibilities:Traffic Analyzer Intelligence builds a composite index of "quintuple + timestamp + session ID".In addition, it can complete accurate retrieval from petabyte-scale historical traffic in seconds; path drawing intelligence automatically constructs a complete attack chain based on causal inference and Bayesian algorithms; depth research intelligence evaluates the actual scope of influence of the threat; security expert intelligence automatically generates an analysis report that contains key evidence and remediation recommendations; and analyst intelligence generalizes and judges the alarms and generates work tasks. Through this collaborative model, manual traceability work that would have taken 8-12 hours can now be completed in 30 minutes, increasing traceability efficiency by 94%.
In-depth analysis of technical architecture
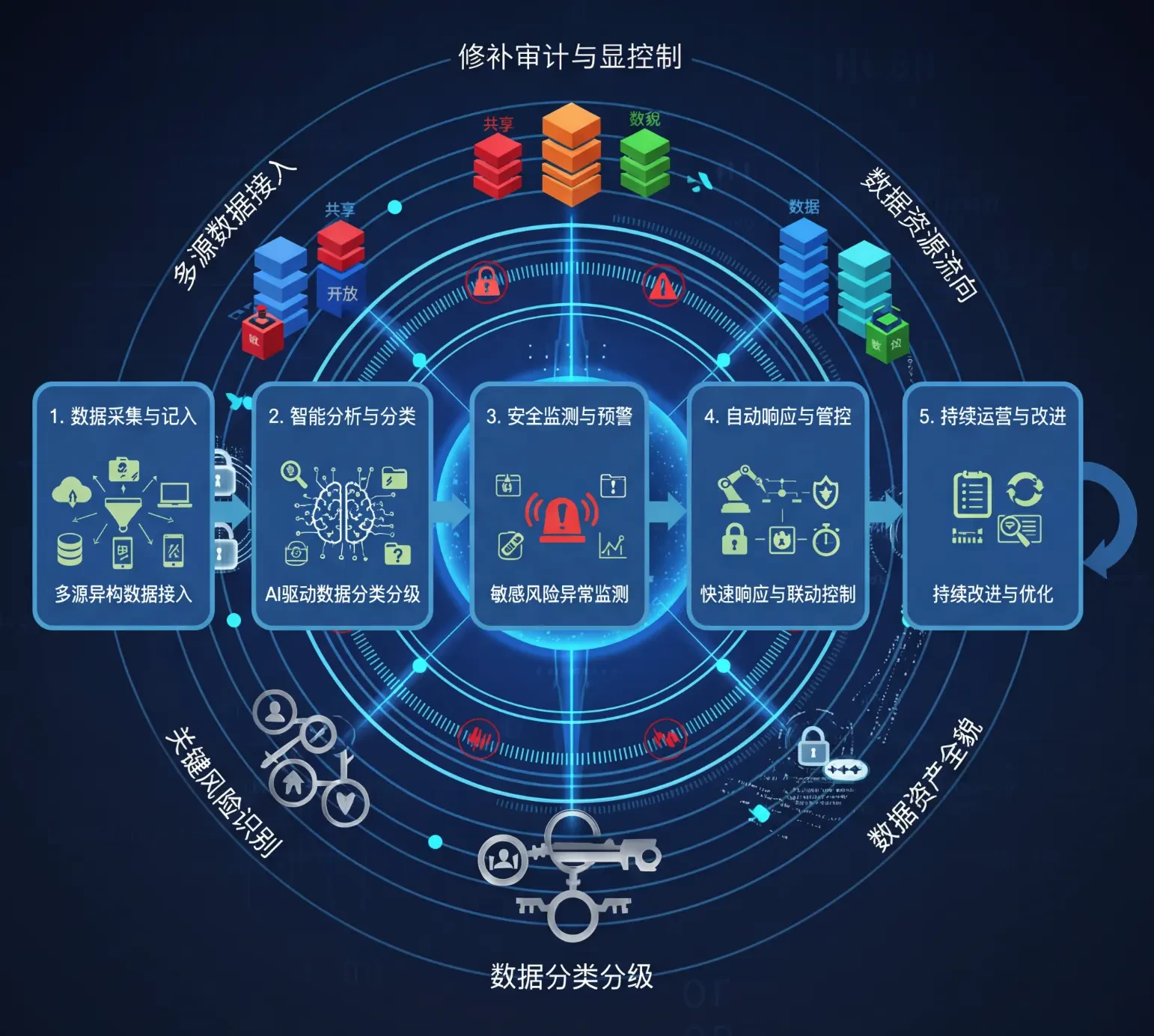
Multi-dimensional security system with layered protection
The country's first Data Security Intelligence utilizes a proven layered protection architecture that applies different security mechanisms at each stage of the data flow. The architecture is categorized into five key layers from bottom to top.
Infrastructure layer:Provides multiple protection with physical isolation, network isolation and virtualization isolation. Minimizes the attack surface through VPC isolation, subnet segmentation and micro-segmentation techniques.
Data storage layer:Implement encrypted storage, access authentication and audit trail for static data. The system uses the AES-256 algorithm to encrypt sensitive data and realizes secure key rotation and isolation through key management services (KMS).
Application Processing Layer:The triple defense of parameterized query, input validation, and output filtering prevents application layer attacks such as SQL injection, command injection, etc. LLM is strictly sandboxed at this layer, and the generated code needs to be dynamically type-checked and privilege-checked.
Intelligent Analytics Layer:Deploys an AI-driven anomaly detection and threat profiling engine to score and categorize all data access behaviors in real time. The system is capable of recognizing high-risk patterns such as anomalous downloads, permission transgressions, and batch queries.
Audit of the governance layer:Records all data access, modification, and sharing behaviors to form a complete audit chain. In the event of a security incident, the audit log can support complete event re-enactment and responsibility tracing.

Convergence Architecture for LLM and Security Knowledge Base
The core competence of the first data security intelligence in China lies in the deep fusion of a general-purpose large language model with a vertical domain security knowledge base. The system adopts a hybrid knowledge enhancement architecture.
Parametric knowledge:The training data incorporates structured security knowledge such as national standard systems (GB/T 35273, GB/T 40857, etc.), industry best practices, and attack signature libraries.
Non-parametric knowledge:Through the RAG (Retrieval-Augmented Generation) mechanism, the system can dynamically invoke external knowledge bases, including real-time threat intelligence, known vulnerability databases, regulatory policy texts, and so on.
Interpretability guarantees:The ability for systems to clearly articulate the reasoning process when making security decisions is critical to meeting audit compliance and gaining user trust. With a SHAP-like approach to model interpretation, security teams can understand why an AI system makes a particular protection decision.
The advantage of this architecture is that when a new type of threat emerges, the system does not need to retrain the entire model, but only needs to update the knowledge base and adjust the Prompt to quickly adapt to the new security scenario.
Benchmarking analysis of key core competencies
Intelligent threat detection capabilities
China's first Data Security Intelligence reaches industry-leading levels of accuracy and speed in threat detection. The detection technologies used by the system include.
Anomaly detection based on behavioral analysis:Baseline modeling using time series analysis (ARIMA, Prophet) can identify even very weak behavioral deviations
Content-based identification of sensitive data:Combining natural language processing and computer vision to recognize sensitive content such as PII, keys, source code, etc. in structured and unstructured data
Association-based identification of high-risk links:Automatic construction of causal relationships between events and identification of multi-step attack chains through graph neural network techniques
Compared with traditional DLP products that can only recognize known sensitive data types, the system's recognition coverage has reached more than 99%, and the false alarm rate is controlled within 0.5%, which is at the international advanced level.
Dynamic and adaptive protection mechanisms
The problem faced by traditional static security policies is that once attackers find loopholes in the rules, they can bypass the protection for a long time. The first data security intelligence in China uses a dynamic adaptive protection strategy.
Feedback-based strategy optimization:The system uses reinforcement learning algorithms to dynamically adjust the weights of the protection rules by continuously monitoring the actual effectiveness of the protection policies to ensure that the protection policies match the current threat environment.
Confrontational defense training:The system has built-in adversarial machine learning capabilities to predict potential ways to bypass the protection and fortify relevant defenses in advance.
Multi-dimensional real-time decision making:When suspicious behavior is detected, the system is not a simple "allow/block" binary decision, but based on user identity, operation content, operating environment and other multi-dimensional factors, to make gradient response decisions, including requiring additional authentication, recording high-risk operations, limiting the rate of access and so on.
Practical application scenarios and effect verification
APT Traceability Applications for the Financial Industry
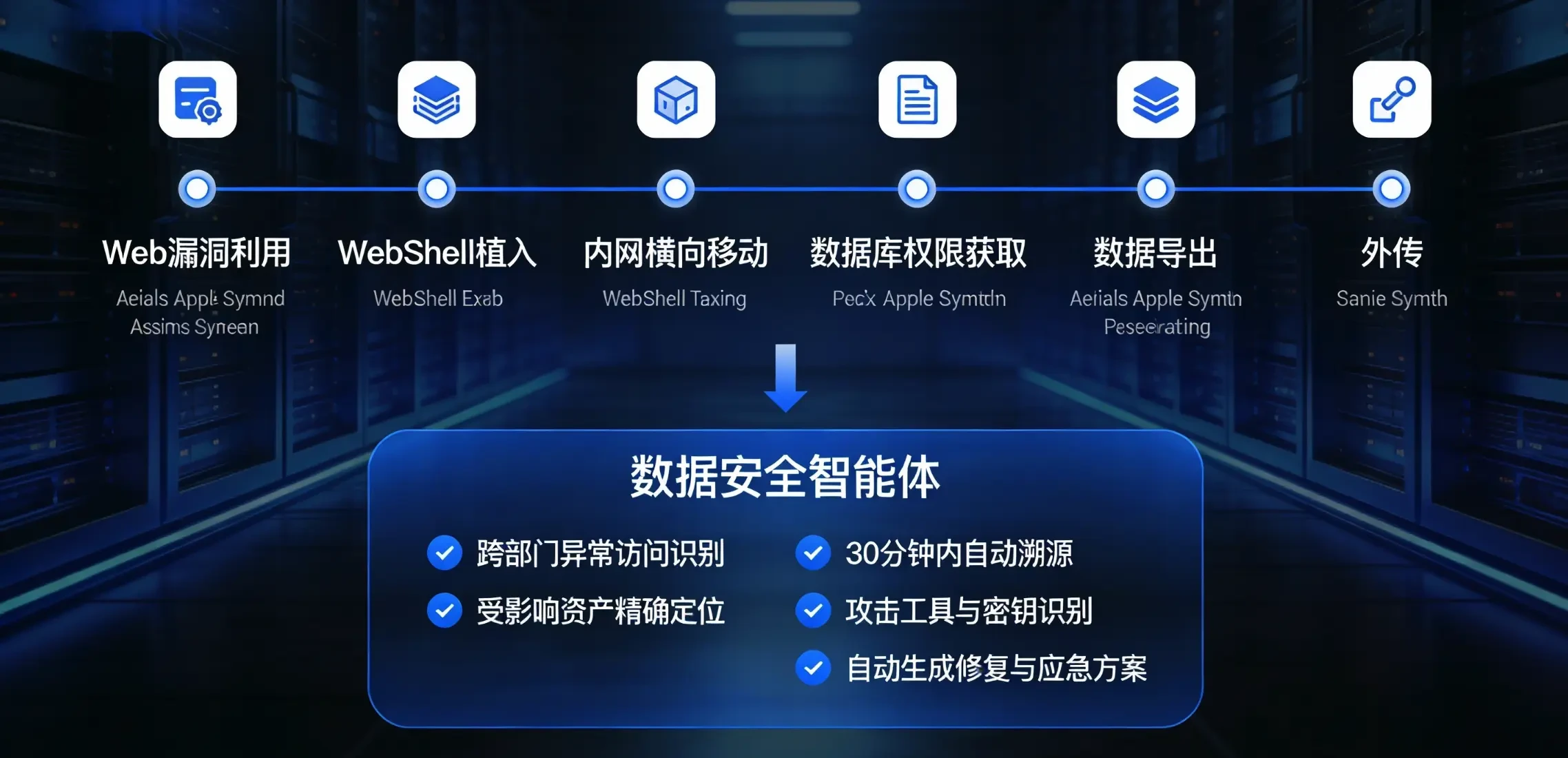
In the actual application of a financial institution, the first data security intelligence in China demonstrated excellent capabilities in the face of advanced persistent threats (APT). When the attacker obtained internal employee credentials through social engineering for lateral movement of the intranet, the system quickly identified abnormal cross-departmental data access behavior and completed it within 30 minutes through an automated traceability process.
Identification of the complete attack chain (from Web vulnerability exploitation → Webshell implantation → intranet lateral movement → database privilege acquisition → data export → outbound)
Precise location of affected assets and data
Identification and decryption of tools and encryption keys used by attackers
Automated generation of remediation recommendations and emergency response programs
This response rate is more than 20 times faster compared to traditional security operations, dramatically narrowing the time window for a data breach.
Patients in the healthcare industryprivacy protection
In the application of healthcare industry, the core challenge of the first data security smart body in China is how to protect patients' privacy while supporting the rational use of data by clinicians and researchers. The system's solutions include.
Automated Sensitive Data Recognition:The system is capable of automatically recognizing a wide range of sensitive fields such as patient name, ID number, case number, diagnostic record, etc. without manual intervention.
Dynamic desensitization strategies:Depending on the identity of the visitor and the purpose of access, the system automatically applies different levels of desensitization policies. For example, financial staff accessing patient data can only see anonymized charge information, while the attending physician can see the full consultation record.
Fine-grained operational privilege control:The system not only controls "who has access to what data", but also "what is allowed" (viewing, exporting, printing, downloading). Some sensitive data is restricted to "read-only" access, and even some operations require secondary authentication or approval from the Medical Ethics Committee.
With this solution, a medical group's patient data breaches were reduced from an annual average of 8-10 incidents to zero, while clinical productivity instead increased by 30%.
Multidimensional Data Governance for the Consumer Goods Industry
In retail and consumer goods organizations, data security challenges stem from the high degree of data fragmentation and frequent collaboration between business units. Results from the adoption of the country's first Data Security Intelligence by a headline brand enterprise include.
Constructed a data security template library for 1000+ business scenarios, covering various scenarios such as sales analysis, supply chain collaboration, membership management, etc.
Permission allocation is automated from manual approval, the approval cycle is shortened from 7 days to 2 hours, and the precision of permissions is improved from "table level" to "field level".
Complete traceability of sensitive data operations, with a complete audit trail of every access, modification, and export of member data, meeting the compliance requirements of the GDPR and the Personal Information Protection Act
Data breach risk downgraded from "high risk" to "manageable", internal data misuse incidents down 75%
Benchmarking with and beyond traditional programs
Compare the functional advantages of DLP products
Traditional data loss prevention (DLP) products, which were once the standard for enterprise security protection in the 2010s, face a core limitation.
| comparison dimension | Traditional DLP Products | Data Security Intelligence |
| Detection method | Based on regular expressions and blacklists | Based on deep learning and big language modeling |
| Threat identification time | Hindsight analysis, hours behind | Real-time recognition with <100ms latency |
| Unknown Threat Protection | Nothing to do but defend against known threats. | Unknown threats can be predicted through anomaly detection |
| Rights Management | Static rules, difficult to adapt to business changes | Dynamic Adaptive with Context-Aware Support |
| false positive rate | 15-25% | <0.5% |
| operating cost | Need for a large number of security specialists | Degree of automation >90% |
| regulatory compliance | passive response | Proactive compliance with GDPR/HIPAA support |
These comparisons fully demonstrate that the first domestic data security intelligences represent a new generation of technical paradigms for data protection.
Advancements over traditional security operations centers
Traditional Security Operations Centers (SOCs) strongly rely on the expertise and experience of human analysts. The bottlenecks it faces include.
Shortage of specialists:The salary of senior security analysts in the market has reached more than 500,000 dollars per year, and small and medium-sized enterprises can not afford such costs. The first data security intelligence in China can replace the labor cost with software cost, which improves the economy by more than 10 times.
The response time is too long:Traditional SOCs typically take 4-8 hours to analyze a medium-complexity security event, a time window that is far from adequate in the face of advanced threats. This intelligent body system has been able to reduce the response time to less than 30 minutes.
Difficulties in knowledge transfer:The experience accumulated by experts is difficult to encode and pass on, and once an expert leaves the organization, he or she faces knowledge loss. The Big Language Model parametrically encodes security expertise and best practices, ensuring knowledge continuity and scalability.
Security and Compliance Assurance
Multi-layered security authentication mechanism
China's first data security intelligence body in the design of the full consideration of the LLM itself exists in the "Hallucination problem" (Hallucination), that is, the model may generate seemingly reasonable but actually wrong content. For this reason, the system adopts a multi-level verification mechanism.
Input validation layer:Strict sandboxing and taint tracking of all inputs from external sources prevents injection attacks.
Process Validation Layer:In the reasoning process of LLM, the system requires the model to show the complete reasoning steps by means of Chain-of-Thought and Tree-of-Thoughts, which facilitates manual review and problem localization.
Output validation layer:The safety decisions generated by LLM need to be validated by the expert system before execution, and important decisions need to be manually confirmed.
Post hoc validation layer:The system continuously monitors all security operations performed and immediately rolls back or escalates the processing level if problems are detected.
This multi-level validation ensures that even if there is an error in the LLM, it does not directly lead to a security failure of the system.
Regulatory Compliance Built-In Design
China's first data security intelligences are fully integrated into various regulatory compliance requirements at the architectural design stage.
Data classification hierarchy:Referring to GB/T 35273, GB/T 40857 and other national standards, the system has built-in automated data classification and grading engine.
Completeness of the audit trail:The system records the entire life cycle of all data collection, transmission, storage, use, sharing and destruction, and generates audit logs that meet the requirements of international regulations such as GDPR and HIPAA.
Technical measures for privacy protection:Technologies such as differential privacy and homomorphic encryption ensure that personal privacy is not compromised even when data is legitimately used for AI training.
The Continuing Evolution of Compliance:The system supports dynamic updating of compliance policies, eliminating the need to modify the core system and simply updating the knowledge base when regulatory requirements change.
Conclusions and future perspectives
The country's first data security intelligences by combining big language modeling, multi-intelligence collaboration, and privacy computing,Zero Trust Architectureand other cutting-edge technologies are integrated to realize theEnterprise Data ProtectionA revolutionary upgrade of the paradigm. Compared to the traditional passive, static, manual-dependent protection system, the system has:
Proactive: Evolving from "remediation after the fact" to "anticipation in advance", with threat detection latency optimized from hours to milliseconds.
Intelligence: The degree of automation exceeds 90%, changing safety operations from "highly labor-intensive" to "self-driven and efficient".
Adaptive: Dynamic and adaptive protection strategies can evolve to follow changes in the threat environment without frequent manual intervention.
Trustworthiness: Multi-level validation mechanisms and a complete interpretable design ensure accurate and auditable security decisions.
Looking ahead, with the further maturation of technologies such as reinforcement learning and federated learning, the first domestic data security intelligences are expected to make breakthroughs in the following directions.
Multi-intelligence cross-organizational collaboration: security intelligences from different organizations can share threat intelligence and protection experience while protecting their privacy
Collaborative defense of cloud-side and end-side: building a collaborative system of cloud-side advanced analysis capability and end-side real-time protection capability
Autonomous Security Adaptation: The system is able to learn and evolve its protection strategies with minimal human intervention.
Overall, the first domestic data security intelligence marks the key shift of data security from "technology-driven" to "AI-enabled", providing a complete solution for enterprises to build a credible, efficient and evolvable data protection system in the AI era.
bibliography
Full-flow security intelligences based on large language models
intelligent bodyAISecurity frameworks and best practices
Microsoft Data Loss Prevention (DLP) Definition and Implementation
Architecture and Application of 360 Security Intelligence
Data Security Intelligence Body Design Patterns and Practical Realization
AWS Data Loss Prevention (DLP) Technical Architecture
2025 Data Security Direction and Intelligent Operations
Volcano Engine Feilian Data Security Product Updates
Data Security Governance Framework and Maturity Assessment
National Standard System for Data Security (2025 Edition)
My blog will soon be synchronized to the Tencent Cloud developer community, and I invite you to join us: https://cloud.tencent.com/developer/support-plan?invite_code=9mtn3hzk7c8
Original article by Chief Security Officer, if reproduced, please credit https://www.cncso.com/en/ai-powered-data-security-agent.html








![[Trial] Ministry of Industry and Information Technology launches emergency response plan for classification and classification of data security incidents](https://static.cncso.com/wp-content/uploads/2023/12/china.webp?x-oss-process=image/resize,m_fill,w_480,h_300,limit_0)