I. Summary of the report
Core views
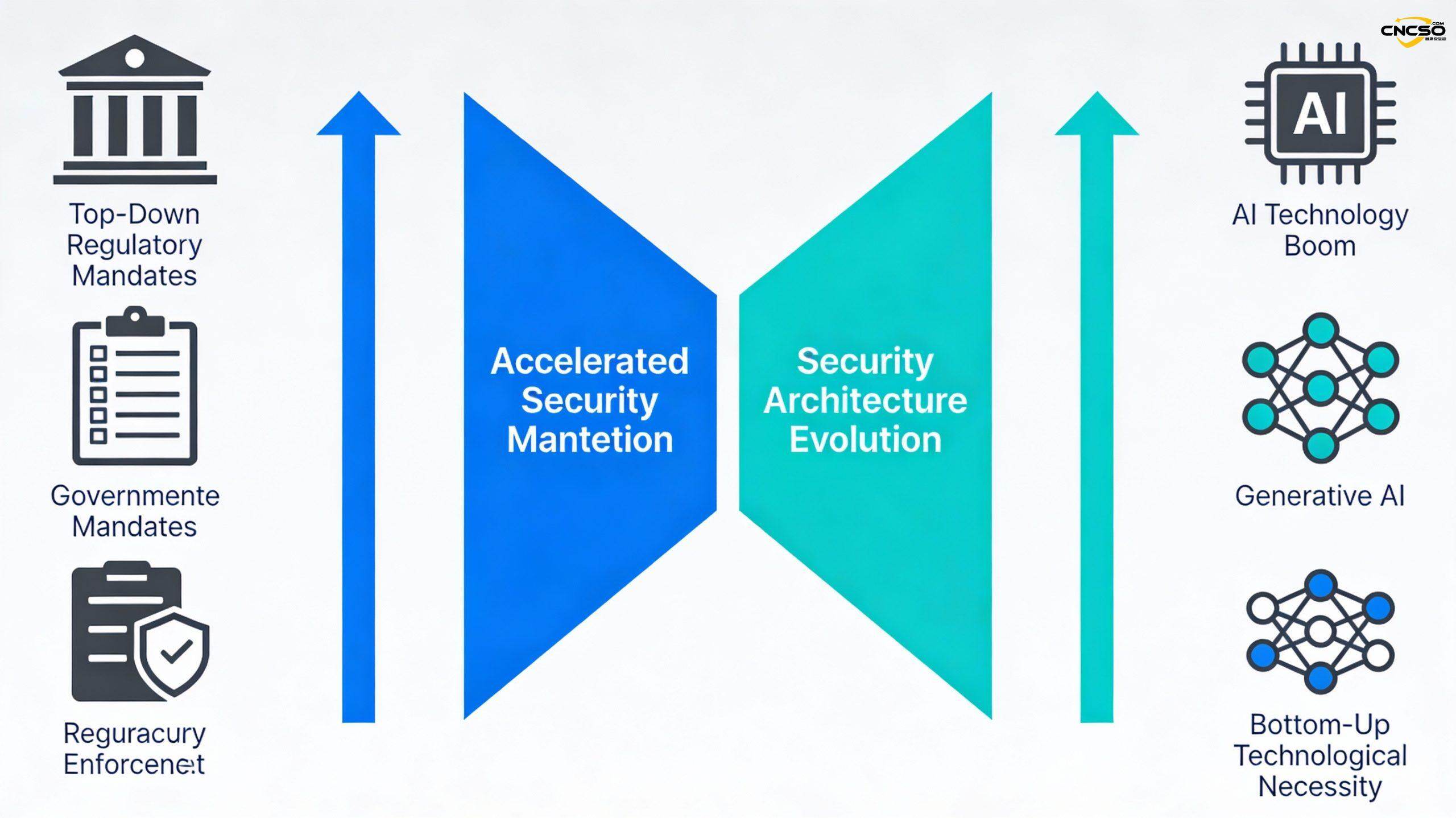
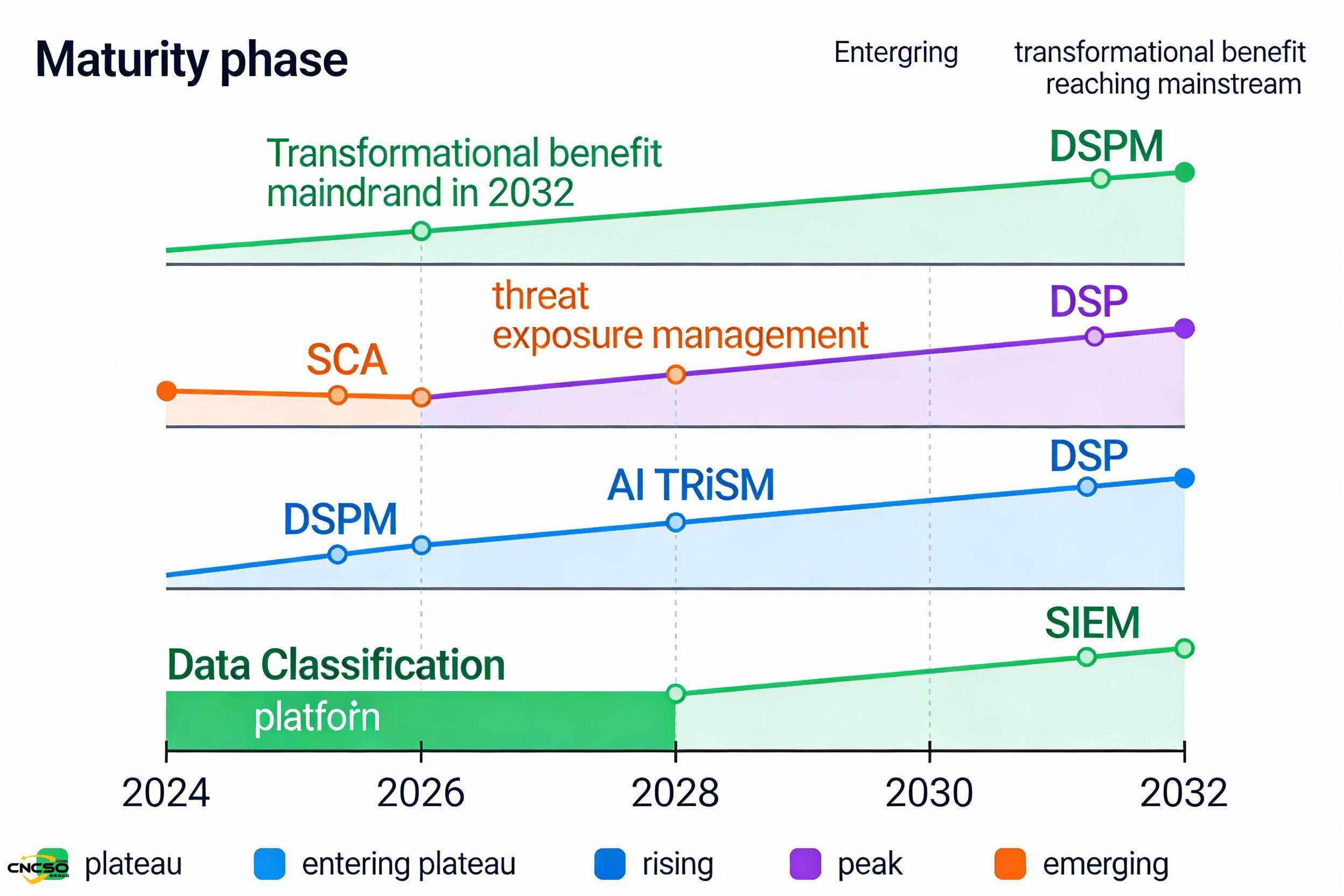
China's cybersecurity sector is undergoing a paradigm shift in 2025. The ”double pressure” of enhanced regulation and explosive adoption of generative AI is shifting the focus of enterprise security from passive compliance and defense to active data governance and AI risk management. According to Gartner's China Cybersecurity Maturity Curve 2025 report, the adoption rate of generative AI is expected to soar from 8% in 2024 to 43%[1], triggering an urgent need for data visibility, AI governance, and threat validation capabilities. This accelerating cycle is driving a new generation of platform-based, data-centric security architectures into the market mainstream.
Core findings of the strategy
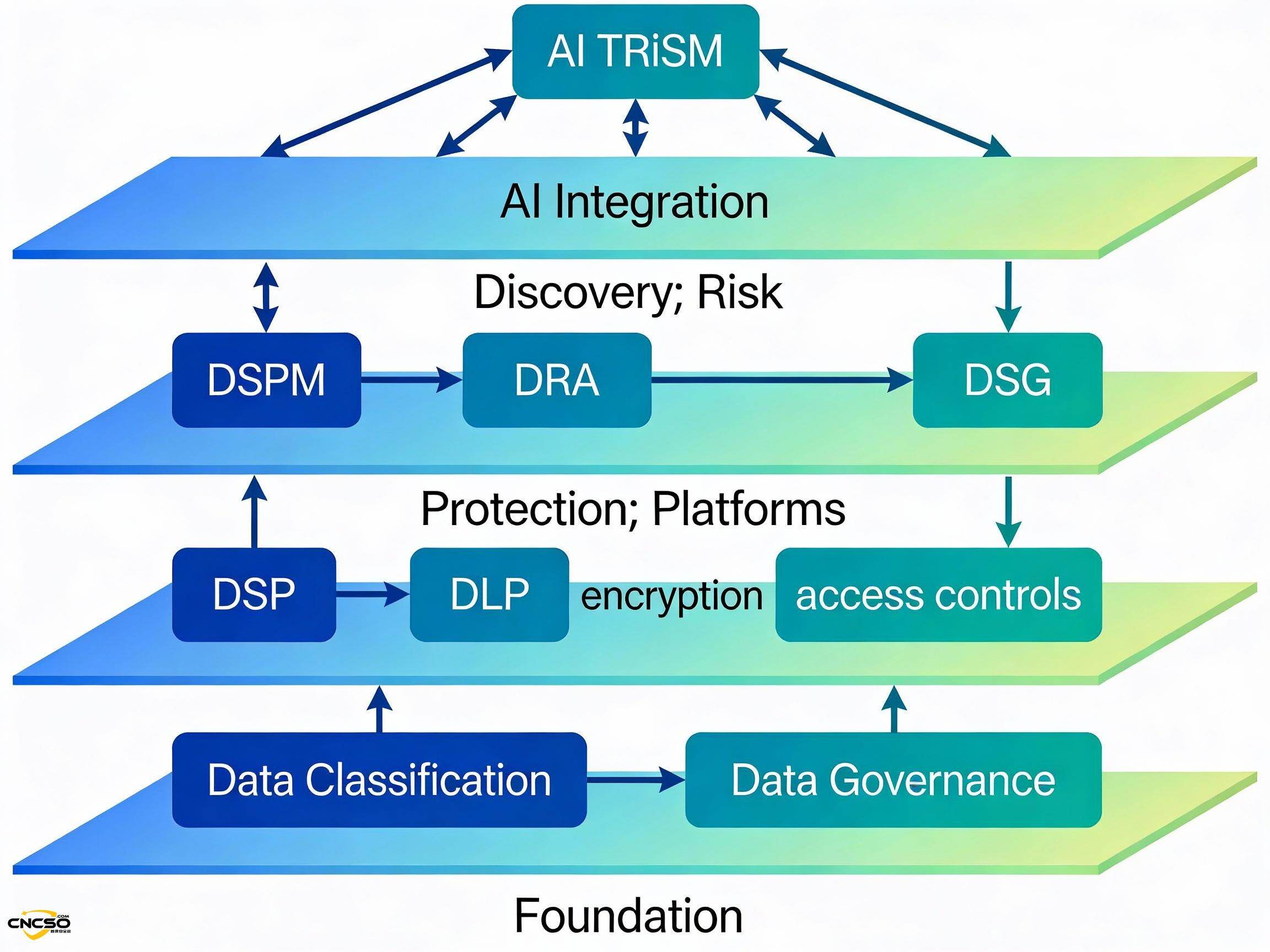
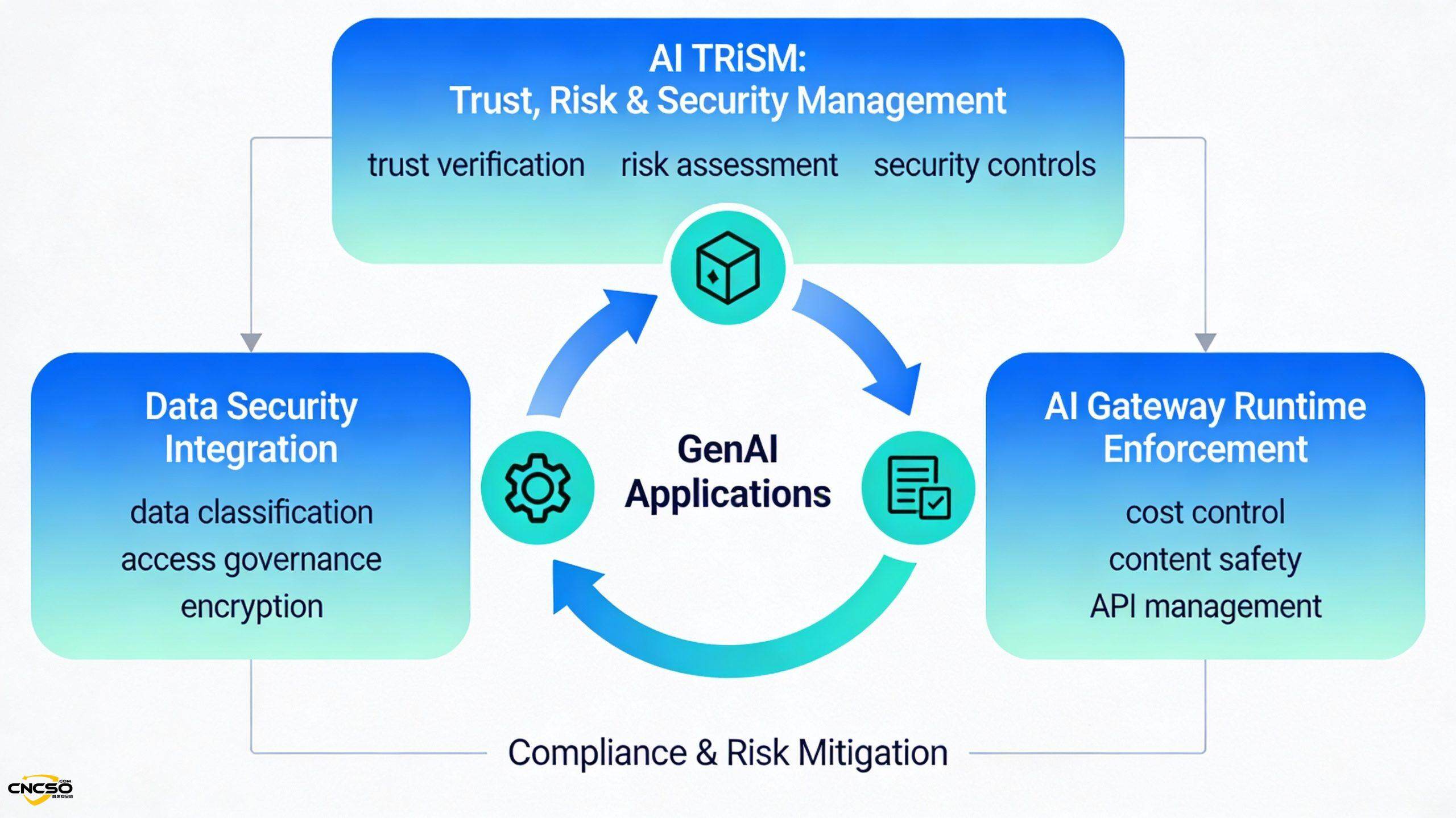
- Data andAI securityIntegration as the main line:Data SecurityThe combination of Dispositional Situation Management (DSPM) and the AI Trust-Risk-Security Management System (AI TRiSM) signals a shift in security investments from basic protection to enabling business innovation, which is a necessary foundation for dealing with the risks of data flooding and AI modeling [1][2].
- Upgrading Threat Management from ”Simulation” to ”Validation”: Adversarial Exposure Validation (AEV) and Exposure Assessment Platforms (EAP) are replacing traditional Attack Simulation (BAS) and Attack Surface Management (ASM) to make the leap from defense optimization to actionable insights that underpin Continuous Threat Exposure Management (CTEM) programs [1].
- Local solutions dominate the market landscape: Influenced by complex certification requirements and geo-friction, local vendors are dominating emerging areas such as DSPM, AI gateways, and threat verification, and the domestic ecosystem is maturing at an accelerated pace [1].
- Security Platform Integration Becomes Imperative: Budget constraints and technology complexity drive SIEM into the platform phase, SASE up, DSPs and EAPs growing rapidly, and enterprises prioritizing the adoption of platform solutions with high levels of integration and a unified toolchain [1].
- Accelerated AIization of Security Operations: Cybersecurity AI assistants are growing rapidly at their peak, filling talent gaps through knowledge aggregation, automation, and agent technology, but need to beware of AI hallucinations and data leakage risks [1].
II. Macro trends: strategic shifts under double pressure
Top-down regulatory enhancements
From 2025, China's data security regulation enters theadvanced stage of implementation. The full implementation of the Regulations on the Administration of Network Data Security and the Measures for the Administration of Data Security in the Commercial Sector not only stipulates the data protection obligations of enterprises, but also creates rigid compliance constraints through rigorous risk assessment, third-party auditing and cross-border transmission review mechanisms [1].
The core features of this regulatory enhancement areSelf-certification mechanisms--Enterprises must continuously demonstrate that their security posture meets regulatory requirements. This is driving organizations to move from ”after-the-fact checking” to ”before-the-fact prevention,” and from black-box compliance checkups to real-time data risk quantification and governance. Technologies such as Data Security Situation Management (DSPM), Data Risk Assessment (DRA), and Data Security Governance (DSG) have emerged as the necessary infrastructure to meet the new compliance era [1].
Bottom-up technical necessity
Meanwhile, the commercial adoption of generative AI has reached a tipping point. The jump in adoption from 8% to 43% reflects strong confidence in the business value of AI [1]. But this confidence comes with a whole new dimension of risk:
- Data leakage channel fission: AI model training, cue word injection, and file uploads have become new vulnerabilities for sensitive data.
- Model risk is unpredictable: The accuracy, ethics, and compliance of AI-generated content face unknown risks and require real-time protection at runtime.
- Risk of cost loss control: Unchecked API calls in token billing mode can lead to exponential cost growth.
The emergence of these risks both requires organizations to protect AI adoption (through AI TRiSM, AI gateways, etc.) and drives organizations to leverage AI to enhance security capabilities (through cybersecurity AI assistants, threat intelligence automation, etc.) [1].
Accelerated Cycles and Market Turns
This dual pressure of ”regulation + technology” is accelerating the evolution of the entire security maturity curve. Certain technologies (e.g., DSPM, AEV, EAP) that would have taken 5-10 years to enter the mainstream are accelerating into commercial adoption because they meet today's pressing needs. The market focus is shifting from basic compliance requirements (e.g., firewalls, intrusion detection) to proactive defense and data-centric security architectures [1].
III. In-depth analysis of focus areas
Area I: Core infrastructure systems for data security
Status and Positioning
Data security has become the most concerned security topic for Chinese enterprises and covers multiple interconnected levels of technology systems. Among them:
- Data Security Situation Management (DSPM): In its infancy, with a revenue rating of ”transformational” [1], expected to mature in 5-10 years, with a market penetration of <1%.
- Data Security Platform (DSP):: On the upswing, with a ”high” benefit rating [1], 2-5 years to maturity, with early adopters already in place.
- Data Risk Assessment (DRA): On the upswing with a ”high” revenue rating [1], 2-5 years to maturity, market penetration 5%-20%.
- Data Security Governance (DSG): Upwardly mobile with a ”high” yield rating[1] and 2-5 years to maturity.
- Data classification: In the platform phase with a ”high” yield rating [1], <2 years to maturity, and has become a required component of the data infrastructure [1].
Core values and definitions
DSPM acts as the ”command center” of the data infrastructure, presenting the security posture and exposure of data in real time through automated data discovery, sensitivity characterization and classification across local data centers, private clouds and multiple local cloud providers. It not only answers the questions of ”what data do I have” and ”who has access to it”, but more critically, ”how does this data flow through my system”. Driven by both the data flood and the demand for AI model training, DSPM has become an essential foundation for organizations to discover shadow data, prevent compliance failures, and unlock the value of AI [1].
Key drivers
compliance pressure: The Network Data Security Management Regulations require organizations to conduct comprehensive risk assessments of data processing activities, especially for third-party sharing and cross-border transmission scenarios.DSPM dramatically simplifies the complexity of compliance proofing through automated data mapping, sensitivity correlation, and access tracking [1].
AI Application Risks: Generative AI adoption has jumped from 81 TP3T to 431 TP3T [1], and organizations urgently need to know what data is safe to use for AI model training, and what needs to be desensitized or quarantined.The integration of DSPM with AI TRiSM serves as the technical foundation for secure data-AI convergence [1].
Multi-Cloud Hybrid Architecture: It is common for Chinese enterprises to adopt a hybrid IT architecture of local + private cloud + multiple public clouds. Traditional isolated data security products cannot provide global visibility across domains, and the value of DSPM lies in unified data mapping and risk quantification [1].
Main challenges and obstacles
Discovery delays: Comprehensive data discovery across complex local, private cloud, and multiple CSP environments can take weeks, especially in Chinese enterprise environments with high legacy system and network segmentation [1].
Integration complexity: The DSPM market has not yet formed a unified metadata standard, and DSPM products from different vendors have their own characteristics, and there are adaptation challenges in integrating with downstream control platforms such as DLP, DSP, and data governance [1].
Limitations in control capacity: Most DSPM vendors are effective at identifying data access risks, but lack sufficient remediation controls and often rely on DLPs, DSPs, or third-party data security functions to perform remediation [1].
Recommendations for action for corporate CISOs
- Prioritize assessment of discovery speed and frequency: Evaluate the fast and comprehensive discovery capabilities and iterative update frequency of DSPM products in typical Chinese enterprise IT environments (including local, private cloud, and local CSPs) to ensure continuous visibility as the data footprint changes [1].
- Integrated pathways for planning and downstream control: Fully evaluate how DSPM integrates with prioritized remediation controls such as Data Loss Prevention (DLP), Data Access Governance, Encryption, and DSP, and prioritize DSPM solutions with open APIs or connectors, taking into account the reality of multi-vendor mashups in the Chinese market [1].
- Using near real-time data stream analysis: Evaluate the ability of DSPM tools to perform near real-time analysis through Data Detection and Response (DDR) techniques, rather than relying solely on point-to-point static analysis. Focus on high-value datasets to reduce analysis overhead and false positives [1].
representative manufacturer
Aliyun, Ambercom, ASIC DAS, Holonet Security, QAX, Sangfor, Tianrongxin, Venustech, etc [1].
Area II: AI security and governance systems
Status and Positioning
AI security has entered a dual-track growth phase in China's cybersecurity market:
- AI TRiSM (Trust-Risk-Security Management): at peak, revenue rating of ”high” [1], 2-5 years to maturity, market penetration 1%-5%. the technology is rising rapidly, key because the emergence of homegrown big models such as DeepSeek-R1 has spiked the volume of AI security inquiries from enterprises.
- China AI Gateway: In its infancy with a ”medium” revenue rating [1], maturing in 5-10 years with a market penetration of 1%-5%, but early feedback from customers shows a strong need for runtime visibility and control [1].
Core values and definitions
AI TRiSM ensures that enterprise AI applications and models behave in accordance with enterprise intent through a four-tier technical capability architecture - AI governance, AI runtime inspection and enforcement, traditional data protection, and privacy protection - while defending against data leakage, third-party risks and undesired outputs [1].
China's AI gateway, on the other hand, is a dedicated tool to address new risks in the process of scaling AI applications. By centralizing the management of API keys, setting rate limits, tracking costs, and intelligently routing multiple LLMs, AI gateways address the dual concerns of enterprises about runaway costs and content security [1].
Key drivers
Data Security Considerations: Enterprise concerns about data breaches, third-party risks, and inaccurate outputs are forcing the adoption of AI TRiSM to ensure that AI behaviors are aligned with enterprise intent, which has become the primary driver for adoption of AI TRiSM [1].
Cost and content control: As generative AI moves from experimentation to scaled adoption, enterprise concerns about cost explosion and content compliance rise. the AI Gateway provides a centralized cost control and compliance enforcement platform for enterprises through Token metering, intelligent routing of requests, and LLM multi-selection management [1].
The Rise of the Domestic Big Models: The introduction of high-performance homegrown models, such as DeepSeek-R1, has stimulated the demand for local AI security solutions in enterprises, which has directly boosted the market attention of AI TRiSM and Chinese AI gateways [1].
Regulatory Compliance Pressure: With the improvement of China's AI governance framework, enterprises need more detailed means of AI runtime supervision to comply with new regulations such as data privacy and content security [1].
Main challenges and obstacles
lag in adoption: Most organizations consider AI TRiSM after the AI application has already entered the production environment, when the cost and difficulty of retrofitting has risen significantly [1].
Skills shortages: The lack of mature AI TRiSM implementation capabilities within organizations often forces them to rely on vendor-provided capabilities, but the market for vendor AI TRiSM solutions itself is still in its early stages [1].
Emerging technologies are unstable: AI gateways are not yet fully validated as an emerging technology and AI requirements are constantly evolving (e.g., Model Context Protocol endpoint management), leading to difficulties in defining requirements [1].
Latency and High Availability: The AI gateway as an intermediate layer introduces latency risk. Enterprises care about time-to-first-token and token throughput, and a single point of failure is an even more necessary consideration for highly available deployments [1].
business-to-business (B2B)CSOproposal
- Forward planning AI TRiSM strategy: Incorporate AI TRiSM considerations at the GenAI application planning and development stage, don't wait until production to retrofit. Establish cross-functional teams (security, legal, compliance, AI development) to define acceptable AI usage policies and embed AI risk management at the governance level [1].
- Development of a run-time governance framework: Establish a discovery, inventory, and governance mechanism for all AI usage (including self-built AI, open source solutions, and SaaS APIs) in the enterprise. Optimize AI gateway architecture to reduce latency risk, ensure highly available deployments, and select vendor solutions with proven disaster recovery and load balancing designs [1].
- Data-AI Security Integration: Ensure that data classification, protection, and access management cover all enterprise information, including unstructured data, so that the datasets accessible to AI have been adequately governed and risk assessed. Integrate AI gateways with Secure Service Edge to enhance AI runtime protection at the endpoint-data-application layer [1].
representative manufacturer
Cisco, DAS Security, Huawei, NSFOCUS, NVIDIA, Palo Alto Networks, Paraview, QAX, Venustech, etc [1].
Domain 3: Threat Exposure and Authentication Evolution
Status and Positioning
Threat exposure management is going through a technology iteration:
- Adversarial Exposure Validation (AEV): On the upswing with a ”high” revenue rating [1], 2-5 years to maturity, market penetration of 1%-5%, replacing traditional BAS.
- Exposure Assessment Platform (EAP): At its peak, with a ”high” revenue rating [1], it has grown rapidly and is replacing traditional ASM.
Core values and definitions
AEV, through automated and continuous adversarial simulation and verification, not only simulates attacks, but more criticallyConfirmation of true availability of exposureIt also highlights the vulnerability paths of critical assets. This marks a paradigm shift from ”peer-to-peer attack simulation” to ”actionable continuous exposure insight” [1].
The EAP provides through an integrated platformPrioritized and actionableVulnerability and misconfiguration views help enterprises target and optimize defenses to support Continuous Threat Exposure Management (CTEM) programs [1].
Key drivers
Compliance DrivenAEV has been able to significantly reduce the cost of red team operations and maintenance through continuous compliance testing and validation, enabling organizations to focus on more complex scenarios [1].
Attack surface complexity: In the era of cloud diversification, containerization, and API explosion, traditional passive asset scanning and vulnerability discovery are no longer sufficient, and continuous, automated verification capabilities of AEVs and EAPs become necessary [1].
Defense Optimization Requirements: Enterprises have begun to adopt AEV to assess the effectiveness of the security controls they have put in place and to automate the optimization of defense configurations through API integration with security tools [1].
Main challenges and obstacles
China Market Gap: Chinese AEV vendors are not yet able to cover all usage scenarios, resulting in purchasers often needing to make trade-offs between coverage and demand matching [1].
Deployment costs: AEVs require significant configuration, customization, and ongoing O&M investment, and are only suitable for organizations with mature security operations capabilities and specialized resources [1].
Cross-team collaboration: The value of AEV relies on the joint participation of security teams, network teams, application teams, and business units. Lack of cross-departmental consensus on value can lead to divergent remediation priorities [1].
Advice to Corporate CSOs
- Integration of CTEM planning: Incorporate existing attack simulations and penetration tests into the CTEM roadmap, progressively increase red team capabilities through automation of AEVs, and prioritize high-impact scenarios and threat intelligence-driven simulations [1].
- Cross-team collaboration and prioritization: Establish a PURPLE TEAMING mechanism to link AEV's modeling data to business impacts, creating a clear prioritization of remediation and gaining buy-in from various stakeholders [1].
- Comprehensive cost-benefit analysis: Evaluate AEV deployment options (cloud-hosted vs. locally deployed) to quantify the value-added compared to traditional vulnerability management and security testing and develop a clear ROI case [1].
representative manufacturer
360 Digital Security, Ant Sword (Beijing Zhiqian Technology), Chaitin Tech, Cyritex, Moyun Technology, TopSec, NSFOCUS, VUL.AI, etc.[1].
Area IV: Security Operations and Platform Integration
Status and Positioning
Security platform integration has become a core requirement for enterprises, with multiple technologies showing divergence:
- Security Information and Event Management (SIEM): In the platform phase, with a ”medium” revenue rating [1], <2 years to maturity, product capabilities have converged, user experience has matured, and it has become a mainstream adoption [1].
- Secure Access Service Boundary (SASE): Rising, with a ”Medium” revenue rating [1], maturing in 2-5 years, growing due to continued demand for network and security integration [1].
- Data Security Platform (DSP):: On the upswing with a ”high” revenue rating [1], maturing in 2-5 years, growing rapidly due to rising demand for data, analytics, and AI pipeline protection [1].
Core values and definitions
These four types of platform-based products reflect the budget-constrained and technologically complex environments in which organizations have a need forUnified visibility and simplified O&MThe urgent need for SIEM. the platform period of SIEM marks its maturity as a security logging infrastructure; the rise of SASE reflects the trend toward network and security convergence; and the rapid growth of DSPs and EAPs suggests that data and exposure management has become a priority investment [1].
Key drivers
Budget constraints and complexity pressures: Security teams in Chinese enterprises are generally understaffed and the existing toolchain is fragmented, resulting in a heavy O&M burden. The need for consolidation forces enterprises to evaluate the ROI of a unified platform [1].
Data Value Unlocked: Enterprises realize that data is the new competitive advantage, but traditional siloed data security products can't support data analytics and AI innovations.DSPs make data sharing more secure and controllable through centralized policy definition and enforcement [1].
Accelerated digital transformation: The acceleration of enterprise digital transformation and AI adoption is placing new demands on the agility and reach of security architectures. platform-based products such as SASE and SSE adapt to this demand [1].
IV. Interpretation of the technology strategy prioritization matrix
Based on the Gartner Prioritization Matrix, organizations should use a phased technology adoption strategy [1]:
Immediate focus (<2 years to maturity)
Data classification and SIEMIt has entered a mature and mainstream phase and is a must-have component of enterprise security infrastructure. The focus is on unlocking its greater value in compliance, auditing, and AI governance through tighter integration with emerging platforms such as DSPs, DSPMs, and DLPs [1].
Medium-term critical (2-5 years to maturity)
AI TRiSM, privacy governance (Privacy in China), SASE/SSE, DSP, DRA, AEVThese technologies have a ”high” benefit rating and are a priority for medium-term strategic investment. These technologies can deliver significant benefits in data governance, AI risk management and business transformation, and organizations should set aside resources for pilots and deployments in their medium-term planning [1].
Long-range layout (5-10 years to maturity)
DSPM, Software Component Analysis (SCA), Threat Exposure ManagementThese technologies have ”transformative” benefits, but market penetration is <1% and implementation experience is limited. Enterprises should continue to build energy for future scale deployment through continuous proof-of-concept and small-scale pilots, while working with vendors to drive ecological maturity [1].
V. Conclusions and strategic recommendations
Core insights for Chinese companies
In 2025 and beyond, Chinese companies will face three major strategic shifts in their cybersecurity buildup:
- From reactive compliance defense to proactive risk governance: Improvements in regulatory systems require companies to move from after-the-fact auditing to ex ante prevention, which means a shift in investment focus from traditional boundary protection to data discovery, risk assessment, and ongoing governance [1].
- From technology silos to platform integration: The flood of data, AI adoption and the emergence of AI models have made single-point tools no longer able to cope. Platformized and integrated solutions (e.g., DSPs, SIEM+ integration, SASE ecosystems) have become necessary to help improve efficiency in the context of talent and budget constraints [1].
- From a defensive posture to empowering innovationThe ultimate goal of security is not to ”stop” but to ”enable business innovation with controlled risk”. This is driving organizations to view AI TRiSM, data security platforms, etc. as business gas pedals rather than cost centers [1].
Advice for Chief Security Officers (CSOs)
Immediate action items (plateaued or peaked)
- Deploying or upgrading SIEM: Ensure that it is integration-ready with the latest DSPM, DRA, AEV and other tools to lay the foundation for unified threat visibility.
- Launch of data classification and DSG project: Using the Network Data Security Management Regulations compliance as an entry point, establish an enterprise data map and governance framework to provide a foundation for DSPM, DSP, and AI applications [1].
- Planning the AI TRiSM pilot: Incorporate AI trust-risk-security considerations at the GenAI application planning stage to avoid the high cost of after-the-fact remediation [1].
Planning pilot projects (on the upswing and high yield)
- DSPM Proof of Concept: Conduct DSPM pilots in business units with high data volumes and complex multi-cloud hybrid environments to assess its real-world effectiveness for data discovery, risk quantification and proof of compliance [1].
- AI gateway trials: Deployment of AI gateways for departments with centralized GenAI applications for cost metering, content security, and multi-LLM management to gain operational experience [1].
- AEV and CTEM integration: Incorporate existing penetration tests and attack simulations into the CTEM framework to gradually automate the verification process through AEV [1].
- DSPs and Data Privacy Protection: Evaluating the integration capabilities of DSPs in data encryption, desensitization, and access control to lay the groundwork for deployment at scale [1].
Continuing concerns (potential for change but needs time to mature)
- SCA and Supply Chain Security: As open source models and AI components grow, software component analysis will become critical. Establishing the preliminaries for internal capability assessment and external vendor selection [1].
- Privacy Enhancing Technologies (PETs): In high-risk scenarios such as cross-border data transmission and multi-party computing, the maturity and usability of technologies such as Trusted Computing and Multi-party Computing are continuously evaluated [1].
- IoT authentication: As enterprise IoT and industrial IoT deployments expand, device identity and authentication mechanisms will become critical defense points [1].
future outlook
The Chinese cybersecurity market will exhibit the following evolutionary tone during 2025-2027:
Technical aspects: The deep integration of data security and AI security will become the core of the next-generation security architecture. The trend of platformization, automation and AI enablement will continue to strengthen, and the market space of single-point tools will be squeezed.
regulatory level: The regulatory framework will continue to improve, especially in the areas of AI governance, cross-border data transfer and privacy protection, resulting in more detailed compliance requirements, which will further accelerate the commercialization of emerging security technologies [1].
Localization level: The market dominance of local vendors will be further consolidated due to certification complexity and geographic considerations. Meanwhile, the product innovation ability of local vendors in emerging areas (DSPM, AI gateway, AEV, DSP) is rapidly improving, and is expected to form internationally competitive solutions [1].
Corporate Security Officers (CSOs) should use this as an opportunity to reimagine their security portfolios to meet the regulatory and risk needs of the present, but also to lay out for a data-driven and AI-enabled business future.
bibliography
[1] Gartner. (2025, July). Hype Cycle for Cybersecurity in China, 2025 (G00828354).
https://www.gartner.com/en/documents/6677034
Analysts: Anson Chen, Angela Zhao, Feng Gao, Mia Yu.
Original article by Chief Security Officer, if reproduced, please credit https://www.cncso.com/en/trends-in-ai-cyber-security-risk-governance-for-2025.html