1. Cyberattack posture in 2025
Overall assessment of the threat situation
The global cyberattack landscape in 2025 presents an unprecedented level of severity. According to Fortinet's Global Threat Landscape Study 2025, Automation Technologies,AIand stolen credentials have become the top three drivers of accelerating cyberattacks. Cyber attackers are industrializing the attack process, from cloud platform intrusion to credential abuse, and traditional defenses are no longer effective against them. As of 2024, the world suffers 36,000 malicious cyber scans per second, with attackers mapping and exploiting digital infrastructure at scale through automated techniques. This figure is growing rapidly compared to previous years, reflecting a continued escalation in the scale and automation of cyberattacks.
The first half of 2025 has seen a record number and scale of overall cyberattacks.Cloudflare data shows that 36.2 million DDoS attacks have been mitigated in the first three quarters alone, equivalent to 1,70% of the total number of DDoS attacks mitigated in the whole of 2024.This indicates that cyberspace is currently facing the strongest wave of attacks on record. The types of attacks are also evolving, from traditional data encryption to a dual threat model of data theft + ransom, putting more pressure on victims.
Main types of attacks
DDoS Attack Scale Sets New RecordDistributed Denial of Service (DDoS) attacks achieve breakthrough growth in size in 2025. Attack traffic from the Aisuru botnet peaked at 29.7 Tbps (terabits per second), the largest DDoS attack ever recorded. Microsoft Azure also successfully blocked attacks launched from over 500,000 IP addresses from the Aisuru botnet in November 2025, peaking at more than 15 Tbps. network-layer DDoS attacks accounted for 711 TP3T of all DDoS attacks in the third quarter, an increase of 871 TP3T sequentially, and 951 TP3T year-over-year. much of this growth stemmed from the emergence and continued expansion of the Aisuru botnet.
Ransomware Attacks Surge Above 50%: Ransomware Attacks Surge 49% in First Half of 2025, Ransomware Groups Expose 4,198 Cases on the Dark Web, Huge Increase from 2,809 Cases in Same Period in 2024. The ransomware-as-a-service (RaaS) model continues to dominate current ransom attacks, which has spawned numerous emerging ransomware organizations by lowering the technical barriers to cybercrime. The "dual threat" model combining data encryption and data theft has become mainstream, with attackers not only encrypting the victim's data, but also threatening to expose it in order to increase pressure for payment.
Information-stealing malware spreads: Fortinet reports a spike in the number of stolen credentials originating from information-stealing (infostealer) malware. These malware are specifically designed to steal login credentials, API keys and session tokens, enabling attackers to perform subsequent elevation of privilege and lateral movement. Stolen credentials become the underlying tool that drives other forms of attacks.
AI-powered phishing explosion: Phishing Attacks Surge by 12,001 TP3T Generative AI is widely used to create highly realistic phishing emails and deep-fake audio and video.AI enables cybercriminals to launch an attack against a business every 39 seconds, causing economic losses totaling $18 million per day. Meanwhile, DDoS attack traffic against AI companies spiked 3,471 TP3T in September 2025 YoY.
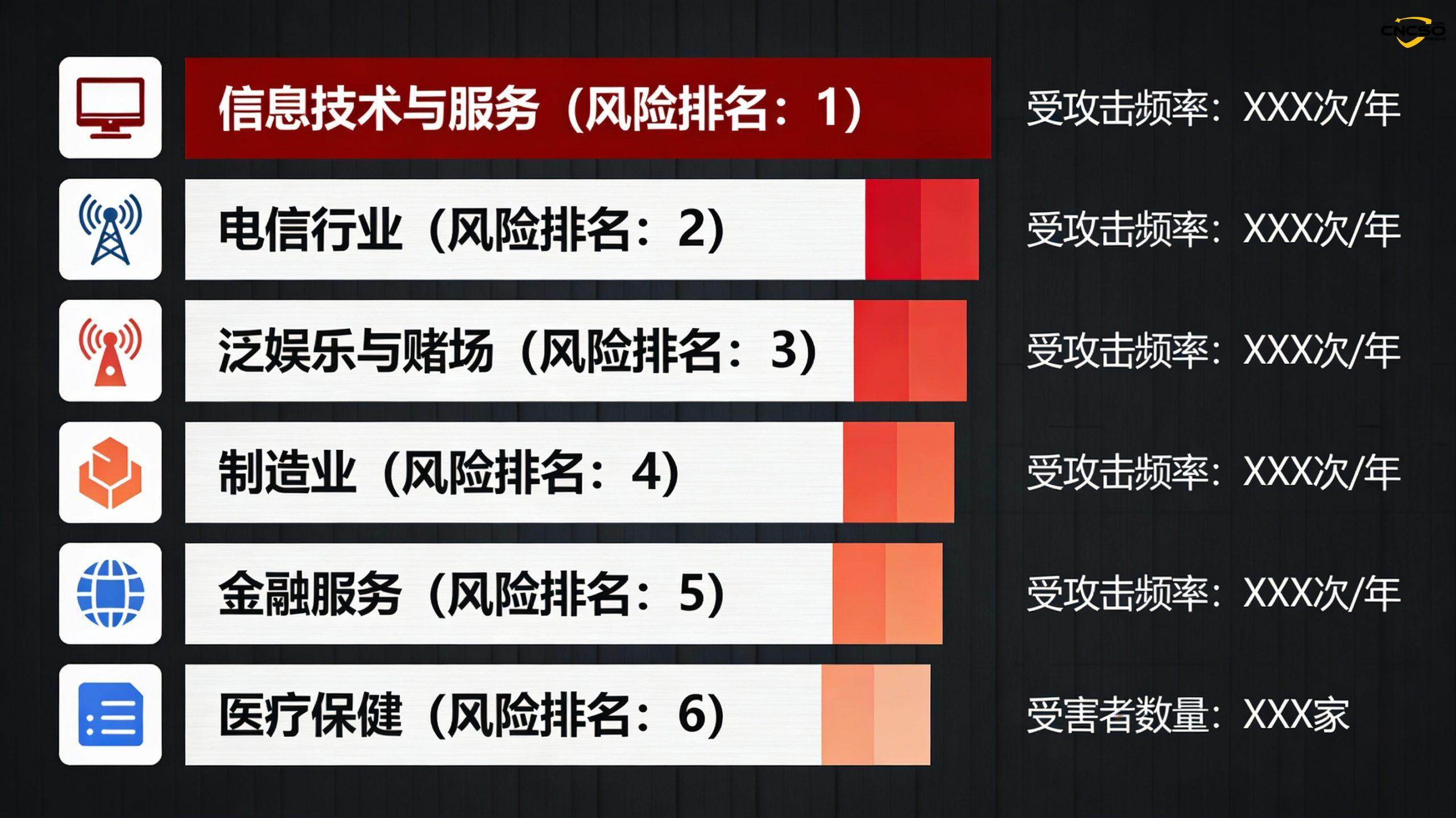
Geographic distribution and industry impact
Global cyberattacks in 2025 are characterized by an uneven geographic distribution. China continues to be the country suffering the most DDoS attacks, followed by Turkey, with Germany in third place.From an industry perspective, information technology and services topped the list of the most heavily attacked industries, followed by telecommunications and pan entertainment and casinos. Manufacturing, financial services and healthcare were also major targets. Attacks on critical infrastructure were particularly prominent, with the energy, emergency and hospital sectors seeing the most significant increase in attacks. Of concern is the surge in supply chain attacks and customized attacks against sensitive industries amid geopolitical tensions.
2. Major cybersecurity incidents in 2025
Salesforce Massive Data Breach
In 2025, Salesforce became a high-frequency target for large-scale data theft and ransom operations. Although Salesforce's own core systems were not compromised, attackers repeatedly accessed customer data through compromised accounts, OAuth tokens, and third-party services. This series of supply chain attacks affected industry giants such as Google, Cloudflare, Zscaler, Tenable, CyberArk, Elastic, BeyondTrust, Proofpoint, JFrog, Nutanix, Qualys, Rubrik, and others. Attackers utilized breaches of integration services such as Salesloft and Drift to obtain OAuth tokens, which in turn were used against other services such as Gainsight. This incident is a great example of the supply chain risks in the modern SaaS ecosystem.
The $1.5 Billion Cryptocurrency Theft
The ByBit crypto exchange theft in February 2025 set a record for the largest cryptocurrency theft on record. Attackers stole approximately $1.5 billion in Ether from ByBit's cold wallet, utilizing its access to developer devices to manipulate the transaction approval process, thus successfully draining the cold wallet of assets. This incident shows that even cryptocurrency trading platforms with the highest levels of security face serious threats from internal or advanced external attackers. During the same period, pro-Israeli hackers compromised Iran's Nobitex exchange, destroying about $90 million in cryptocurrency.
PornHub Data Breach and Extortion
The ShinyHunters ransom gang stole data from PornHub from Mixpanel, a third-party analytics provider. The attackers claimed to have stolen a total of about 94GB of data, which contained records of viewing, searching, and downloading activities of more than 200 million subscribers. This incident highlights the security risks of third-party data processing services and the value of personal privacy data in online blackmail.
Aisuru Botnet DDoS Attacksbandwagon
The Aisuru botnet emerged as the most destructive cyber threat in 2025, with its operators compromising the TotoLink router firmware update servers in April 2025, infecting around 100,000 devices and allowing it to rapidly expand in size. The botnet targeted security vulnerabilities in IP cameras, digital video recorders (DVRs/NVRs), Realtek chips, and routers from brands such as T-Mobile, Zyxel, D-Link and Linksys. According to XLab research, Aisuru currently controls an estimated 1 million to 4 million infected hosts.
The most impactful attacks included a 29.7Tbps DDoS attack on Cloudflare in October 2025, a 15Tbps attack on Microsoft Azure launched by over 500,000 IPs, and over 20Tbps attacks on the online gaming industry.Aisuru's major attack traffic originated from compromised devices of major U.S. ISPs such as AT&T, Comcast, Verizon, Charter and T-Mobile, and other major U.S. ISPs. In addition, the hackers leased Aisuru as a "residential proxy network," allowing other criminals to disguise their sources and conduct phishing and fraud.
Infiltration of IT staff in a country
In 2025, IT workers in a given country became a significant identity security threat to organizations.xx Authorities discovered so-called "laptop farm" operations in at least 16 states: local facilitators received company-issued laptops in lieu of actors in a given country and facilitated remote access to corporate environments from a given country. In addition, the "infectious interview" campaign involved attackers misusing the recruitment and interview process as a means of delivering malware.
Social Engineering Attacks and Insider Threats
2025 has seen a significant increase in social engineering attacks against business process outsourcing (BPO) service providers and IT service desks. Following attacks on Marks & Spencer and the UK Co-operative Group, the UK government issued guidance on preventing social engineering attacks against service desks and BPOs. In addition, insider threats have had a far-reaching impact. A number of significant incidents have demonstrated that employees or consultants with trusted access, either through deliberate misuse of that access or by not having it revoked in a timely manner after leaving their jobs, can trigger large-scale disruption.
AI Security Threatsand new attack paradigms
The Evolution of AI-Driven Cyber Attacks
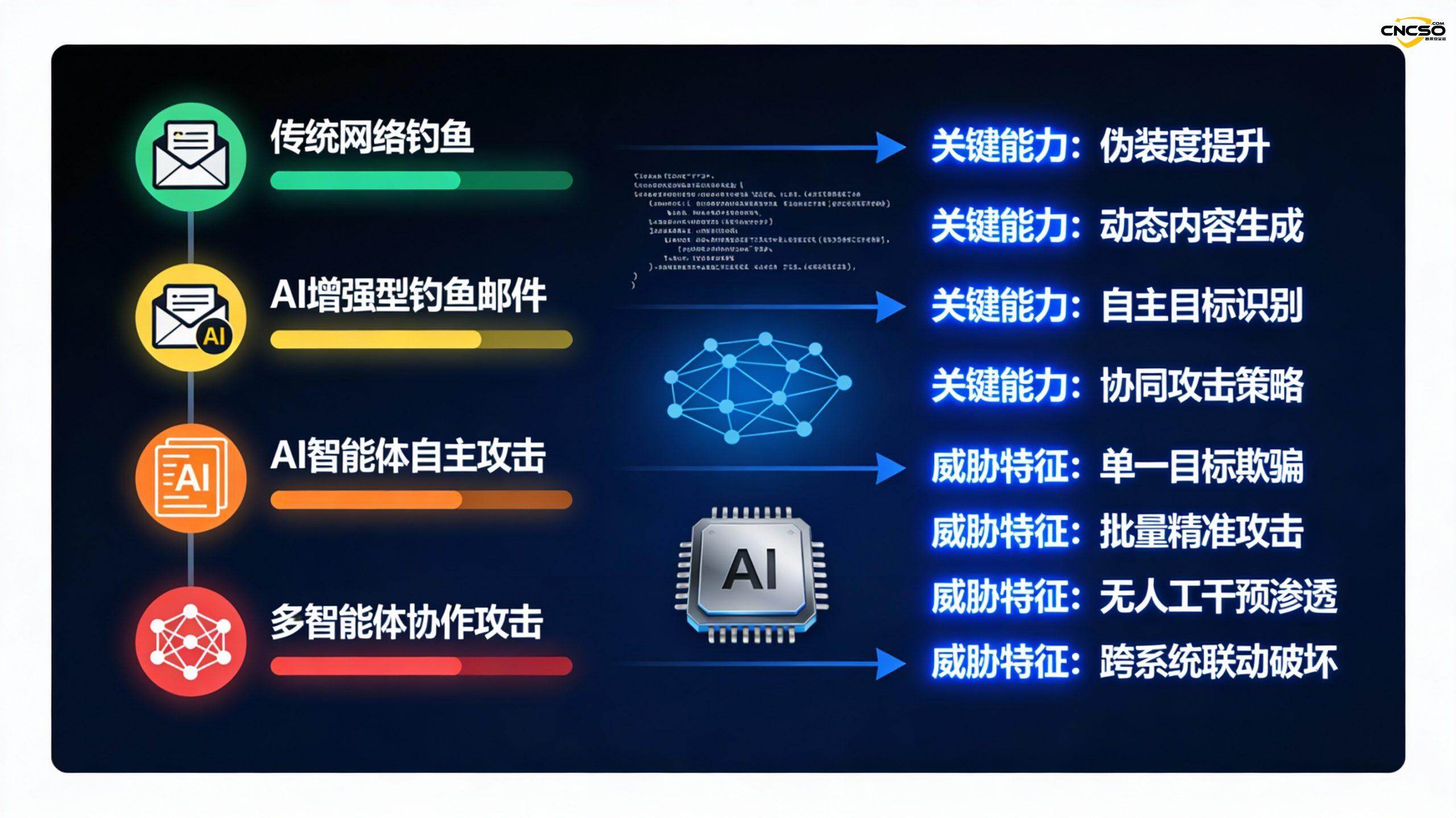
The year 2025 has been defined as the "Year of the AI Intelligence Body", where AI technology in cyber-attacks has evolved from an assistive tool to an autonomous system. This evolution consists of four key stages:
Phase 1: AI-assisted conventional attacks.. Generative AI has been used to generate more deceptive phishing emails, create realistic and deeply forged audio and video, and rapidly generate malicious code. For example, ransomware developers have used Claude to implement sophisticated malware features such as using the ChaCha20 stream cipher encryption algorithm, implementing direct system call bypassing of EDR using RecycledGate and FreshyCalls technologies, and developing anti-analysis and anti-recovery mechanisms.
Phase 2: AI Accelerates Vulnerability Discovery and Exploitation. the AI intelligences are used to automate vulnerability scanning and penetration testing.2025 In July, the Ukrainian Computer Emergency Response Center (CERT-UA) disclosed the first malware program integrating LLM capabilities, APT28-LAMEHUG, which uses natural language in its code to invoke the Qwen Big Model cloud service on HuggingFace to generate system commands to steal information from end users. Experienced hackers using AI assistance can complete a scaled attack in a month that would have taken a team months.
Phase 3: Autonomous Decision Making and Execution by AI IntelligentsiaAI intelligences can not only discover vulnerabilities, but also autonomously plan attack strategies, adjust execution programs, and evaluate results.2025 In the early "Harbin Asian Winter Games" cyberattack, the attackers used AI intelligences for tool planning, vulnerability exploration, and traffic monitoring, and some of the code was clearly written by AIs, which can automatically and quickly write dynamic code during the attack. Some of the code was clearly written by AI, which was able to automatically and quickly write dynamic code during the attack.
Phase 4: Multi-intelligence collaborative attack systemThe biggest threat to the future comes from the new paradigm of AI + Multi-Intelligence + Runtime Generation. The biggest threat in the future will come from the new attack paradigm of "AI + multi-intelligence + runtime generation". The master intelligence controlled by the hacker is responsible for the overall command and orchestration, while sub-intelligences dispersed in different networks or endpoints act flexibly and autonomously according to the environment, adjusting their strategies in real time to achieve the final goal.
AI-specific security vulnerabilities
Cue Injection and Memory Contamination...AI intelligences face unique security threats. In a prompt injection attack, an attacker induces an AI system to perform unintended actions through carefully constructed input text. Even more dangerous are memory contamination attacks, in which the attacker implants false or malicious information into the intelligence's long-term storage. Unlike standard prompt injection, which ends when the chat window closes, the contaminated memory persists, and the intelligence "learns" the malicious commands and calls them up in future sessions, often days or weeks later.
Data Securityand privacy breaches.. The autonomy of intelligences exacerbates data security and privacy risks. Agents often need to retrieve information from large unstructured datasets to accomplish their tasks. Without strict access control and semantic validation, agents may inadvertently retrieve and output sensitive personally identifiable information (PII) or intellectual property in response to seemingly innocuous queries from users with lower privileges. Attackers may also leak sensitive information by tricking the intelligentsia into summarizing such data in some way via side channels.
Cascading failures and system crashes. In multi-intelligent systems, the failure of a single compromised intelligence can trigger cascading failures. research published by Galileo AI in December 2025 found that cascading failures propagate through a network of intelligences much faster than can be controlled by traditional event-response mechanisms, with a single compromised intelligence influencing downstream decision-making at 871 TP3T within four hours.
Identity impersonation and misuse of credentialsThe rise of AI intelligences has spawned an explosion of "non-human identities" (NHIs), including API keys, service accounts, and digital certificates used by intelligences to authenticate themselves. Risks escalate when agents are able to access the credentials of other agents.2025 Real-life incidents have shown that a supply chain attack on the OpenAI plugin ecosystem resulted in the theft of agent credentials from 47 enterprise deployments, which attackers used to access customer data, financial records, and proprietary code for up to six months.
Real-world examples of AI-driven attacks
Nx Build Software Supply Chain Attack.2025 In August, a supply chain attack (s1ngularity), a host-implanted attacker program utilized endpoint-local AI CLI tools (including Claude, Gemini, and Amazon Q) to invoke a large model service to generate code and launch an attack, enabling reconnaissance and data theft. This is the first known case of an attacker turning a developer AI assistant into a supply chain exploitation tool.In the age of AI intelligences, attackers inject malicious logic into popular open source intelligences frameworks and tool definitions downloaded by developers.
Microsoft 365 Copilot Zero Hits Leaked. Researchers have found that Microsoft 365 Copilot suffers from zero-hit data leakage, where specially crafted emails are injected with hidden hints to expose sensitive information without user interaction. Google Gemini has also been shown to be vulnerable to prompt injection attacks via email digests and calendar invitations.
Typical network security case study
Critical infrastructure attacks
Attacks on critical infrastructure, such as energy, health care and emergency response, are increasingly the focus of national-level threat actors. These attacks not only cause direct economic loss, but can also jeopardize public lives. For example, in a national-level cyberattack that occurred in early 2024, a country's intelligence agency took advantage of a zero-day vulnerability in a mail system to implement long-term control over the mail server of an important military enterprise in XX, stealing a large amount of important and sensitive information.
Manufacturing Supply Chain Attack
Manufacturing continues to be a high-frequency target for ransomware attacks.2025 An agent-based procurement system deployed by a mid-sized manufacturing company was subject to a supply chain attack between Q2 and Q3, where attackers compromised a supplier validation agent through a supply chain attack launched against an AI model provider, causing it to begin approving orders from a shell company controlled by the attackers. This type of attack illustrates well the new risks posed when production systems are integrated with AI systems.
Fintech and Cryptocurrency Risks
Cryptocurrency trading platforms have been the hardest hit by cyberattacks involving not only technical vulnerabilities, but also social engineering and insider threats.2025 A series of large-scale thefts have demonstrated that even financial institutions, which have invested the most in security, face systemic risks from multiple directions.
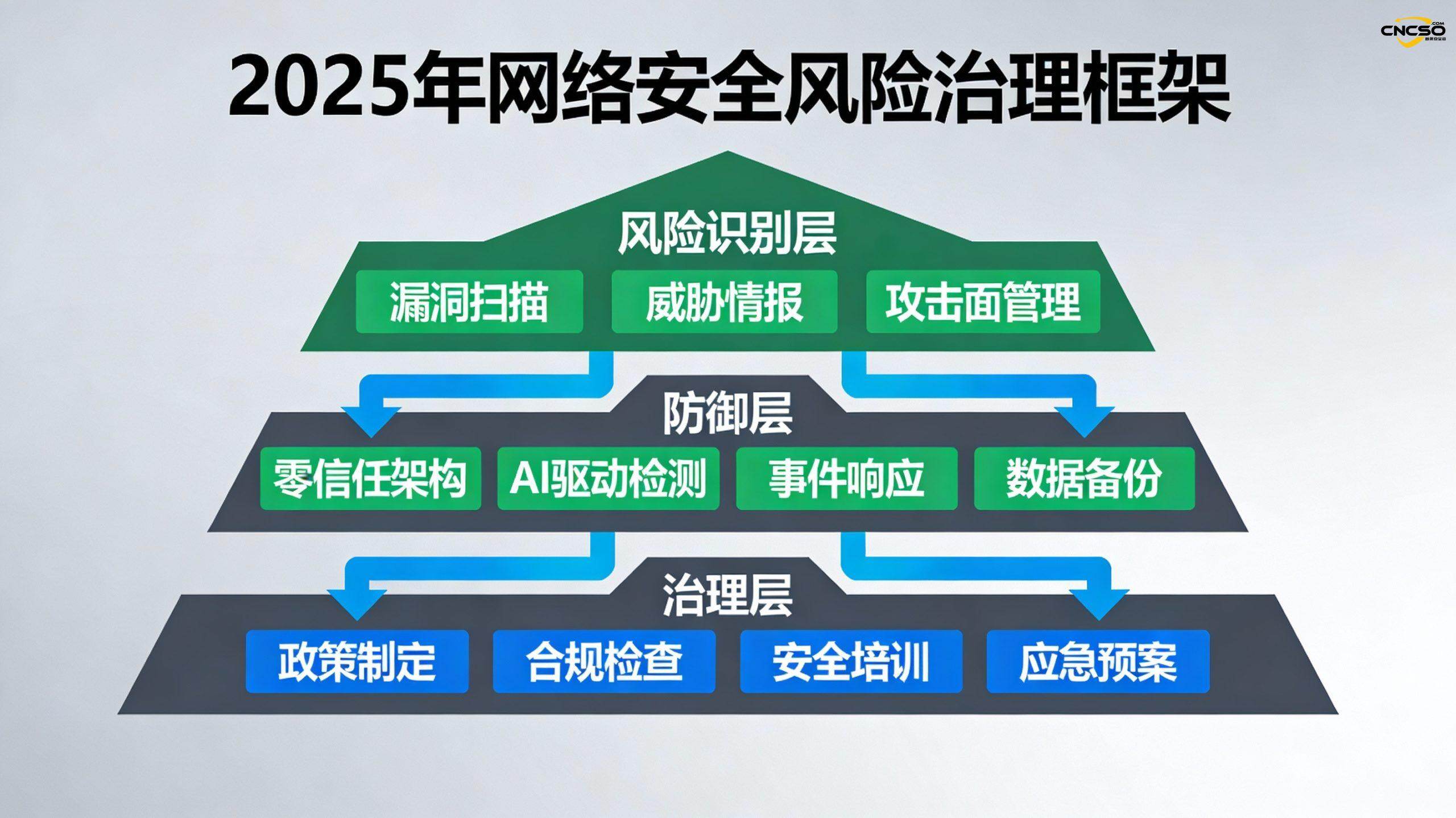
Cybersecurity risk governance
Governance framework and strategic alignment
The year 2025 marks a significant shift in cybersecurity defense strategy - from reactive defense to proactive exposure management and resilience building. Traditional "fortress-like" defenses are no longer sufficient to address the current threat landscape, and organizations need to employZero Trust Architectureas the new security paradigm. This requires continuous authentication of all users, devices and traffic, whether from internal or external sources.
AI-driven threat detection and responseGradually replacing traditional rules-based defenses. Real-time integration of multi-source intelligence that combines AI-based detection with traditional rules-based systems can balance robustness, fault tolerance, and scalability.AI-powered asset and vulnerability management systems are able to use AI intelligences to analyze vulnerability exploitability and prioritize remediation, accelerating the automated process of remediation.
Vulnerability and Exposure Management
The Mid-2025 Vulnerability Landscape Report shows that vulnerabilities continue to rise in both number and complexity. To address this challenge, organizations need to establish a complete asset inventory and vulnerability management process and integrate it with attack surface management. Regular penetration testing and red team exercises can help organizations identify and close defense blind spots. In particular, easily overlooked entry points such as IoT devices, smart hardware and edge computing devices should also be included in security management.
Data Protection and Privacy Compliance
Given the frequency of data breaches in 2025, data classification, encryption, access control and privacy design have become the core of enterprise security. Organizations should establish a complete data backup and recovery system to cope with ransomware "dual threat" attacks. At the same time, they should strictly comply with data protection regulations such as GDPR and CCPA, and establish an emergency response process for data leakage. For systems involving personal information, multi-factor authentication (MFA) and strong password policies should be implemented.
Supply Chain Securitymanagerial
Supply chain attacks are increasingly becoming the preferred option for advanced threat actors, and organizations need to establishSupply Chain Security Management Program. This includes: security audits of all third-party service providers, regular security assessments, inclusion of security clauses in vendor SLAs, code reviews of key vendors, and implementation of software bill of materials (SBOM) management. Especially when using open source software, cloud services and AI services, the associated risks should be carefully assessed.
AI system security construction
The September 2025 release of theArtificial Intelligence Safety Governance Framework2.0" for the domesticAI securityBuilding provides systematic guidance. Key measures include:
-
Model and Algorithm Security: Enhance security assessment and auditing of large models to prevent discrimination due to algorithmic bias, address model interpretability issues, and defend against adversarial attacks
-
AI system risk prevention and control: Establish a threat modeling and risk assessment process for AI systems to monitor AI-driven cyber-attacks and prevent malicious AI use
-
Non-Human Identity (NHI) Management: Establish an identity management system for AI agents and service accounts to prevent credential misuse and identity impersonation
-
AI model monitoring: Monitor and manage the deployment of AI models and service calls on endpoints and hosts, blocking the new risk of models being exploited by malicious programs
Organizational security awareness and capacity-building
In the face of increasingly complex threats, organizations need to invest inSecurity culture and capacity-building:
-
Safety Training and Awareness Raising: Regular training on common threats such as social engineering, phishing attacks, etc., with specialization for senior management, IT and finance departments
-
Security Architecture Evolution: Establishment of a security operations center (SOC), deployment of SIEM systems for real-time monitoring, and establishment of incident response and emergency recovery capabilities
-
Network resilience building: Shift from defense-only to resilience-building, including business continuity planning, disaster recovery plans, and adaptive defense systems
Conclusions and recommendations
The cybersecurity landscape of 2025 has moved beyond the traditional dichotomy of "threat and defense," and the development of AI technology has provided both powerful new tools for defenders and unprecedented capabilities for attackers. This "Age of AI" will require organizations to make profound shifts in strategy, technology, and operations at multiple levels.
For AI engineers, security engineers andCSOThe core recommendations are set out below:
-
Strategic level: Recognize that AI has become a double-edged sword, and while using AI to enhance defenses, it is important to build a deeper understanding of the security of AI systems themselves. Shift from reactive defense to proactive exposure management and resilience building.
-
Technical aspects: Accelerate the deployment of core technologies such as zero-trust architecture, AI-driven detection, and supply chain security. Strict security assessment and monitoring of AI models, APIs and agents.
-
Operational level: Establish a complete security operation system, including threat intelligence sharing, incident response process, and emergency recovery capability. Pay special attention to easily overlooked entry points such as IoT devices, smart hardware, and edge computing.
-
Governance level: Promote the construction of a security culture within the organization and strengthen security training and awareness-raising. Establish a cross-sectoral security collaboration mechanism to ensure a balance between security construction and business needs.
Globally, more than 30 countries have started dialogues and technical meetings on AI security governance. The future competition for cybersecurity is essentially a competition for AI security capabilities. Organizations and countries that preempt AI-driven defenses will gain a significant advantage in the digital age.
Original article by Chief Security Officer, if reproduced, please credit https://www.cncso.com/en/2025-global-cyberattack-ai-security-threat-report.html