1. Introduction
The composition of Internet traffic is fundamentally changing under the wave of digital transformation. Themalicious robotThe Report brings us up to date on the latest developments in the automation threat.The 2025 report is particularly compelling, with data that suggests we are at a critical turning point-...automated flowsurpassed human-generated traffic for the first time, with a share of 511 TP3 T. This landmark change, largely driven by theAI(AI) and Large Language Models (LLMs), driven by their popularity, have significantly contributed to the scale and sophistication of malicious automated attacks while lowering the barriers to bot development.
The three core topics of the report:
1. The new normal of automated traffic: analyzing the background, composition and far-reaching implications of automated traffic overtaking human traffic.
2.AI-enabledof attack evolution: exploring how AI can fundamentally change the complexity and evasion capabilities of bot attacks.
3. APIs Become the New Focus of Attacks: Analyzes why APIs are rapidly becoming the primary target of malicious bot attacks, and the associated risks and challenges.
Through a systematic analysis of these key areas, this paper aims to provide organizational decision makers andcyber securityProfessionals provide strategic insights and actionable defense recommendations to address this evolving threat landscape.
2. Automated flows overtake human beings for the first time: the threat picture in the new normal
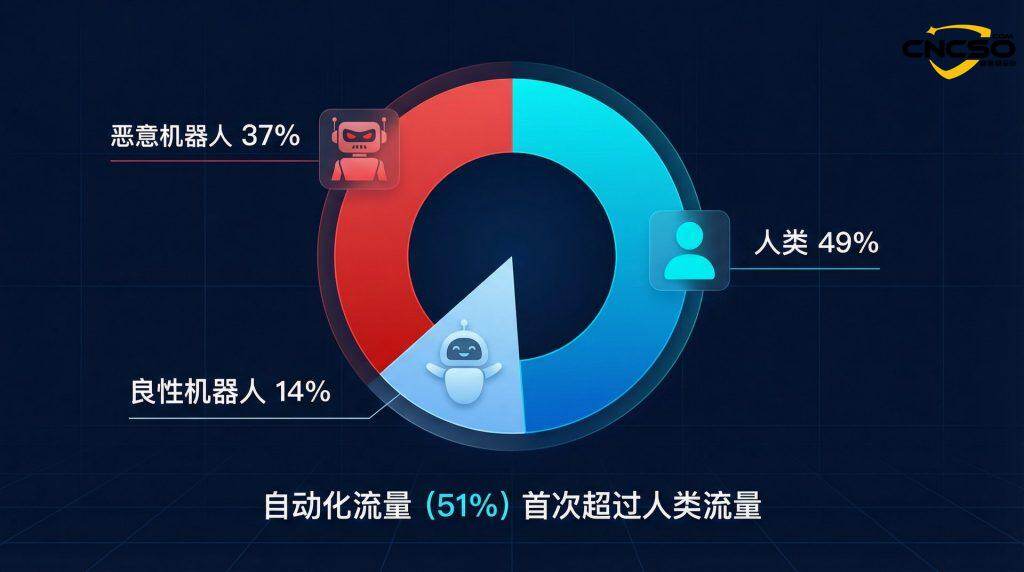
2024 is the yearnetwork trafficA watershed moment in history. According to Imperva's monitoring data, automated traffic (including benign and malicious bots) accounted for 511 TP3T of all Internet traffic, exceeding for the first time the 491 TP3T generated by human users.This phenomenon not only signals a structural change in the Internet's interaction patterns, but also signals that the security challenges faced by organizations are entering a new phase.
As shown in the chart above, global Internet traffic in 2024 is characterized by the following composition: Bad Bots account for 371 TP3T, Human traffic for 491 TP3T, and Good Bots for 141 TP3T. this is the first time in a decade that automated traffic exceeds human traffic in a historical way.
| Type of flow | Share in 2024 | Share in 2023 | annual growth rate |
| Bad Bots | 37% | 32% | +15.6% |
| Good Bots | 14% | - | - |
| Human | 49% | - | - |
Table 1: Global Internet Traffic Composition in 2024
As shown in Table 1, the traffic share of malicious bots has risen dramatically from 321 TP3T in 2023 to 371 TP3T, marking the sixth consecutive year of growth. Behind this growth is the ”democratization” of attack tools. The proliferation of technologies such as generative AI has made it easy for less-skilled attackers to generate and deploy large-scale automated attack scripts, leading to a surge in the number of ”simple” bot attacks. The report notes that simple bot attacks will account for 451 TP3T of all bot attacks in 2024, a significant increase from 401 TP3T in 2023.
At the same time, the combined share of advanced and moderately complex bot attacks is still as high as 55%. These advanced threats are able to more accurately mimic human behavior, use more sophisticated escape techniques, and pose a more direct threat to an enterprise's core business logic and sensitive data. Automated traffic beyond humans means that traditional traffic anomaly-based detection models will face greater challenges, security defense system must shift from focusing on ”whether it is a human” to a more refined ”intent recognition”.
Historical trends show a consistent upward trend in the growth of malicious bot traffic. in 2015, malicious bots accounted for only 191 TP3T of all traffic, whereas by 2024 this number has climbed to 371 TP3T, nearly doubling. Of particular note is a significant growth spike in 2019, largely driven by an unprecedented surge in online usage during the COVID-19 pandemic. This trend continues to this day, demonstrating that malicious bots have become a constant threat that cannot be ignored in the Internet ecosystem.
3. AI-enabled attacks: evolution from ”simple” to ”evasive”
The development of AI technology is like two sides of the same coin, advancing society while providing cyber attackers with unprecedentedly powerful weapons.The 2025 report makes it clear that AI is profoundly altering the ecosystem of malicious bots in the following ways.
The figure above illustrates the AI-driven attack evolution cycle, a closed-loop feedback process from the use of AI tools to bot generation, attack execution, defense detection, and then learning and adaptation. This cyclic mechanism enables malicious bots to continuously optimize their attack strategies and improve their evasion capabilities.
3.1 Lowering the Threshold for Attacks and Expanding the Scale of Attacks
AI-assisted script generation and automation tools have made launching large-scale attacks no longer the preserve of a handful of advanced hackers.Imperva's data shows that its platform blocks an average of 2 million AI-powered attacks per day, with the total number of malicious bot requests blocked for the year totaling a whopping 13 trillion. Behind this, AI tools such as ByteSpider Bot (54%), AppleBot (26%), ClaudeBot (13%), and others are widely used for attacks or camouflage.
In the distribution of AI-driven attack types, custom rule attacks have the highest share (48%), followed bybusiness logic attack(25%) and API violations (16%). This suggests that attackers are leveraging the flexibility and adaptability of AI to customize attack strategies for specific targets, rather than relying solely on generic attack patterns.
3.2 Evolution of Robot Complexity
Attackers use AI not only to generate bots, but also to analyze the success or failure of attacks and continuously optimize their evasion techniques. This has led to the emergence of Evasive Bots, which are more environmentally aware and dynamically adaptable. These robots utilize advancedescape tacticIncluded:
| escape tactic | descriptive | typical case |
| Residential Agents (Residential Proxies) | Attacks are launched using real home IP addresses, making it difficult to distinguish their traffic from normal users. | The 21% ISP bot attack is conducted through a residential proxy. |
| Browser Masquerade (Browser Impersonation) | Mimic the fingerprinting information of major browsers (e.g. Chrome) to bypass simple User-Agent based filtering. | 46%'s bot attack masquerades as Chrome. |
| Bypassing CAPTCHA | Utilizes AI image recognition and machine learning models to automatically solve various CAPTCHAs with high success rates. | - |
| Polymorphism | Bots are able to dynamically change their code, behavioral characteristics, or network properties to evade signature-based detection. | - |
| API Abuse | Attack the back-end API directly, bypassing the front-end's complex security protection and user behavior analysis. | The 44%'s advanced robotic traffic targets the API. |
Table 2: Malicious Robot Core Escape Tactics
As shown in the figure above, bot evasion tactics present a multi-layered architectural system, ranging from basic evasion (e.g., forging browser identities) to expert evasion (e.g., direct API abuse and bots-as-a-service), forming a complete threat ecosystem. The browser forgery statistics on the right further corroborate Chrome's position as the most frequently forged browser (461 TP3T), followed by Mobile Safari (171 TP3T) and Mobile Chrome (141 TP3T).
3.3 Increase in business logic attacks
AI enables bots to better understand and exploit holes in an application's business logic. For example, Denial of Inventory on an e-commerce platform, Seat Spinning on an airline website, or microfinance in a financial application.Payment fraudThe report shows that 25% bot attacks directly target business logic. The report shows that 25% bot attacks directly target business logic, which is usually ”low and slow” and difficult to detect by traditional WAF rules or rate-limiting policies.
Business logic attacks are insidious in that they often mimic the behavioral patterns of normal users, but the intent behind them is malicious. For example, a seemingly normal user may frequently add items to the shopping cart but never check out, thereby tying up inventory resources and preventing real users from making purchases. This type of attack is extremely challenging for traditional traffic rate or signature-based detection systems.
4. APIs: the new battleground for automated attacks
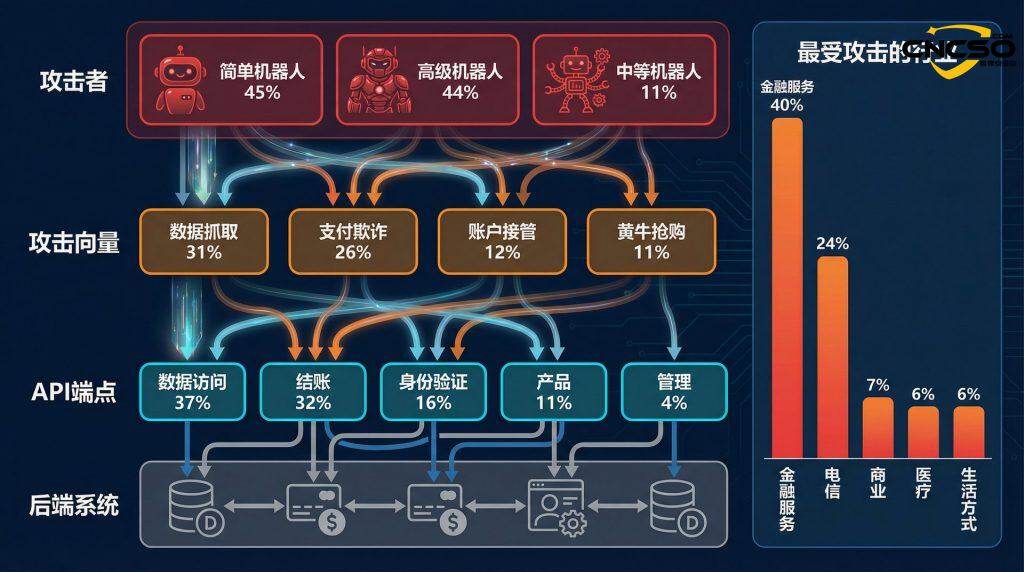
With the popularity of microservice architectures and mobile applications, APIs have become the cornerstone of modern digital business. However, their open and interconnected nature has also made them prime targets for malicious bots. According to the report, 441 TP3T of advanced bot traffic was directed to APIs, compared to 101 TP3T for traditional web applications, a significant difference that highlights the shift in attackers' strategic focus.
The figure above clearly shows the complete architecture of an API attack: from the attacker layer (simple, advanced, and medium bots) to the attack vector layer (data crawl, payment fraud, account takeover, scalping), then to the API endpoint layer (data access, checkout, authentication, product, management), and finally to the backend system layer (database, payment processor, user management system). The industry target distribution chart on the right shows that financial services (40%), telecommunications (24%) and business services (7%) are the most attacked industries by APIs.
4.1 Why have APIs been targeted?
The reasons why APIs are the focus of attacks can be summarized in the following three points:
1. Value centralization: API directly connects back-end data and core business functions, and is the entry point for high-value data (e.g., personal information, payment data) and key operations (e.g., transferring money, placing orders).
2. Relatively weak defense: Compared to mature Web application protection, many enterprises'API securityProtection is not yet perfect, lacking fine-grained access control, abnormal behavior detection and business logic abuse protection.
3. Ease of automation: The structured nature of APIs makes them highly susceptible to automated script calls and abuse, allowing attackers to easily conduct large-scale data grabs, account takeovers, and fraudulent activities.
4.2 Most Attacked Industries and Attack Methods
The report provides an in-depth analysis of API attacks, revealing the most attacked industries and specific attack techniques:
| rankings | The most API-attacked industries | percentage |
| 1 | Financial Services | 40% |
| 2 | Telecom & ISPs | 24% |
| 3 | Business Services (Business) | 7% |
| 4 | Healthcare | 6% |
| 5 | Lifestyle | 6% |
Table 3: Industries Most Attacked by APIs in 2024
In terms of attack techniques, data scraping accounted for the highest percentage at 311 TP3 T. Attackers automate the extraction of large amounts of data by leveraging APIs that expose sensitive or proprietary information. This method is favored because it automates the collection of valuable datasets such as user details, product information, and internal metrics with minimal resistance. Massive data grabs not only facilitate further criminal activity, but may also provide competitive intelligence.
Second is Payment Fraud with a share of 261 TP3T. attackers target financial transaction endpoints to manipulate the payment process in order to commit fraud. This technique involves exploiting vulnerabilities in checkout systems to trigger unauthorized transactions or abuse promotional mechanisms. The direct financial impact, coupled with the erosion of customer trust, makes payment fraud a highly attractive target for malicious bots.
Account Takeover (Account Takeover) Accounting for 12%, attackers use stolen or brute-force broken credentials to gain unauthorized access to user accounts. Once in control of the account, the attacker can access sensitive personal and transactional data, often leading to broader security breaches and further exploitation.
Scalping (Scalping) Accounts for 11% and involves bots quickly purchasing or reserving large quantities of high-demand goods or services. This tactic not only disrupts fair consumer access, but also disrupts market dynamics by allowing attackers to resell these goods at inflated prices.
4.3 Endpoint Specific Attack Analysis
In terms of API endpoints attacked, Data Access has the highest percentage at 371 TP3T.These endpoints are responsible for retrieving sensitive or proprietary information, making them a goldmine for attackers. The high attack rate of approximately 371 TP3T indicates that adversaries are investing heavily in capturing and stealing data. Such data can fuel further criminal activity or serve as competitive intelligence. The attractiveness of data access endpoints stems from the sheer volume and sensitivity of the information they control, often with less stringent security measures than transactional endpoints.
Checkout endpoints account for 32% and are critical for processing financial transactions. These endpoints face about 32% of all API attacks. They are prime targets as any disruption here has a direct impact on revenue and customer trust. Attackers use vulnerabilities to manipulate the payment process, commit fraud, or abuse business logic, leading to unauthorized financial activity. The significant focus on the checkout process emphasizes the need for strong transaction security, including real-time monitoring, layered authentication and proactive fraud detection measures.
Authentication Endpoints (Authentication) Account for 161 TP3T of API bot attacks that promote authentication and access control These endpoints are attacked to bypass multi-factor authentication, abuse token-based authentication, and manipulate session processing. Given their role as the first line of defense in protecting user access, any compromise here could lead to account takeovers and broader vulnerabilities. Strengthening these endpoints with strong dynamic authentication protocols and regular auditing is critical to mitigate the risk of unauthorized access.
Overall, the focus on data access, checkout, and authentication endpoints reflects a careful strategy by attackers to exploit the most critical and vulnerable areas of the API infrastructure.
5. Resurgence of Account Takeover (ATO) Attacks and Industry Implications
Account Takeover (ATO) attacks showed a staggering growth in 2024, with a year-on-year increase of 401 TP3T, and an even bigger increase of 541 TP3T compared to 2022. the report notes that a whopping 141 TP3T of all login attempts were ATO attacks, meaning that users' digital identities are facing unprecedented threats.
5.1 Drivers of the surge in ATO attacks
The surge in ATO attacks is driven by three main factors:
1. Scale of Credential Breaches: The frequency of large-scale data breaches provides attackers with massive amounts of ”ammunition” (username and password combinations). According to the Identity Theft Resource Center (ITRC), more than 1.7 billion data breach notifications were issued in the U.S. in 2024, up 3,12% from 419 million in 2023.
2. Intelligence of attack tools: AI-driven automated tools can efficiently performVoucher Filling(Credential Stuffing) and brute-force cracking, and can intelligently bypass multiple authentication mechanisms such as MFA.
3. Value-driven attack targets: High-value industries such as financial services (22%), telecommunications (18%), and IT (17%) are prime targets for ATO attacks, as successful account hijacking can lead to direct financial gain or theft of sensitive data.
In terms of temporal trends, ATO attacks saw a significant increase in the second half of 2024 (starting in June), with September, October, and November seeing a year-over-year increase in attacks of 791 TP3 T. This increase can be linked to the following factors:
-Seasonal e-commerce and sales events: with major shopping events such as Black Friday and holiday sales peaking in the second half of the year, attackers are targeting high-value accounts during these periods, leading to a dramatic increase in ATO attempts.
-Increase in data breaches: the increase in stolen credentials due to high-profile data breaches provides attackers with a larger database of stolen login information, making it easier to execute ATO attacks.
-More sophisticated attack techniques: Attackers are using more advanced tools such as bots and AI-driven automation to bypass traditional security measures such as CAPTCHA and MFA, leading to a surge in successful ATOs.
5.2 Most ATO-attacked industries
| rankings | sector | percentage |
| 1 | Financial Services | 22% |
| 2 | Telecom & ISPs | 18% |
| 3 | Computing & IT | 17% |
| 4 | Business Services (Business) | 11% |
| 5 | Food & Beverage | 10% |
Table 4: Sectors Most Attacked by ATOs in 2024
The financial services industry has been a prime target for account takeover attacks because of the high value of accounts and the sensitivity of the data to be accessed. Banks, credit card companies and fintech platforms hold large amounts of personally identifiable information (PII), including credit card and bank account details, which can be sold on the dark web for profit. The proliferation of APIs in the sector has expanded the attack surface for cybercriminals who target API vulnerabilities, such as weak authentication and authorization methods, for account takeover and data theft.
The telecom industry is also a prime target for account takeovers, but its motives go beyond financial gain. While access to sensitive PII and customer data can be financially rewarding for attackers, the telecom industry controls critical Internet infrastructure. By compromising the accounts or systems of an Internet service provider or ISP, attackers can intercept or reroute traffic (man-in-the-middle attacks), deploy malware, or disrupt services during times of geopolitical conflict, which is often the target of state actors, who routinely target telecom organizations for espionage and surveillance.
5.3 Consequences of ATO Attacks and Regulatory Penalties
The consequences of an ATO attack can be catastrophic, not only resulting in direct financial loss to users, but also severely eroding a company's brand reputation and potentially triggering hefty regulatory fines. Below are some of the penalties under some of the major regulatory frameworks:
| regulatory framework | Fines | Additional consequences |
| GDPR (General Data Protection Regulation) | Up to EUR 20 million or 4% of global annual turnover | Additional penalties for failure to notify authorities within 72 hours |
| CCPA (California Consumer Privacy Act) | Up to $2,500 per violation, $7,500 for willful violations | Consumer Litigation for Personal Data Exposure, Including Class Actions |
| HIPAA (Health Insurance Portability and Accountability Act) | 100-$50,000 per violation, up to $1.5 million in annual fines | Serious Penalties for Exposure to Protected Health Information (PHI) |
Table 5: Key Regulatory Penalties Associated with ATO Attacks
A successful account takeover attack resulting in a data breach can lead to regulatory penalties, legal fees, indemnification claims, reputational damage and long-term financial losses. The severity depends on the nature of the breach, the regulatory environment and the company's response time.
6. Robotics threats from a global and industry perspective
6.1 Global Distribution of Threats
Globally, the U.S. continues to be the most significant source and target country for malicious bot attacks, carrying 531 TP3T of attack traffic. This phenomenon is not surprising, as the U.S. has the world's largest online economy, with millions of consumer transactions occurring every day. As home to a significant share of global wealth, leading financial institutions, and high-value digital assets, the U.S. offers cybercriminals a wealth of targets to attack.
Brazil and the U.K. tied for second place, each accounting for 6% of all attacks.Brazil's fast-growing e-commerce market and digital financial services, as Latin America's largest economy, make it an attractive target for bot attacks. The UK, as a global financial center and a major digital economy, has a high degree of digitization of its banking, retail and government services making it vulnerable to automation threats.
Canada, ranked third (4%), is also a frequent target due to its strong banking sector, e-commerce growth and digital government services. Bot attacks in Canada typically involve account takeovers, automated fraud, and the grabbing of sensitive data. The country's close economic ties with the U.S. also make it a prime target for cybercriminals seeking to capitalize on cross-border transactions and shared digital infrastructure.
6.2 industry threatlandscape
In the industry dimension, the 2024 data shows some new changes:
The travel industry has become the biggest victim: with 27% of attacks, the travel industry has surpassed the retail industry (15%) for the first time to become the industry most affected by malicious bots in 2024. Attacks such as ”seat rotation” and ”ticket scalping” against airlines not only disrupt the normal ticketing market, but also seriously affect the consumer experience and airline revenue.
| rankings | sector | Share in 2024 | Share in 2023 |
| 1 | Travel | 27% | 21% |
| 2 | Retail | 15% | 24% |
| 3 | Education | 11% | - |
| 4 | Financial Services | 8% | 16% |
| 5 | Business Services (Business) | 8% | - |
Table 6: Most Attacked Industries in 2024
Interestingly, while attacks against the tourism industry were number one in total, the percentage of simple bots in them rose dramatically from 341 TP3T to 521 TP3T, while the percentage of advanced bots fell from 611 TP3T to 411 TP3T.This reaffirms the trend of AI lowering the bar for attacks - more skilled low-skilled attackers are able to use AI tools to launch large-scale simple attacks.
Key threats to the tourism industry include:
-Seat Spinning: bots simulate the booking process up to the payment step, reserving tickets but never completing the purchase, denying real customers access and forcing them to look elsewhere.
-Look-to-Book Ratio Distortion: Excessive robotic traffic inflates the look-to-book ratio, distorting demand and pricing models and putting airlines at a competitive disadvantage.
-Unauthorized Scraping: competitors and fraudsters scraping fare data to influence pricing strategies and revenue management.
-Loyalty Program Fraud: Bots perform credential stuffing attacks to hijack loyalty accounts and redeem stolen rewards.
-Ticket Scalping: Attackers use bots to hoard tickets for high-demand flights and resell them at inflated prices.
Bot attacks against the travel industry grew by 2,801 TP3T from January 2022 to December 2024, highlighting the growing vulnerability of the industry.
Threat complexity varies across industries: the report provides a more targeted risk portrait by analyzing the complexity of bot attacks faced by each industry. For example, the food and grocery industry faces a high percentage of advanced bot attacks of 731 TP3T (501 TP3T in 2023), while the education industry faces 921 TP3T of simple bot attacks.
This difference suggests that different industries need to configure defense strategies with different emphases based on their characteristics. For industries facing advanced threats (e.g., grocery, gambling, sports, entertainment, financial services), more sophisticated behavioral analytics and machine learning-driven detection systems need to be deployed. For industries that face mostly simple attacks (e.g., education, healthcare), threats can be effectively mitigated by strengthening basic security measures (e.g., rate limiting, IP reputation checking).
7. Defense strategies and conclusions
In the face of increasingly severe automation threats, enterprises must build a multi-layered, adaptive defense-in-depth system. Based onImperva Reportinsights, we offer the following core defense recommendations:
7.1 Go beyond traditional WAFs and embrace advancedRobot protection
Relying on IP reputation, signatures or simple rate limiting is no longer enough to deal with modern bots. Enterprises need to deploy specialized bot management solutions capable of granular client fingerprinting, behavioral analysis and intent recognition. These solutions should be able to:
-Real-time identification and classification of bots: distinguishing between benign bots, malicious bots, and human users.
-Behavioral analytics: Monitor user behavioral patterns and identify unusual activity such as rapid succession of requests, unnatural navigation paths, or suspicious transaction patterns.
-Machine learning-driven detection: Utilizes machine learning algorithms to continuously learn and adapt to new attack patterns, improving detection accuracy and reducing false positives.
-Challenge-response mechanism: CAPTCHA or other challenges are applied to suspicious traffic to verify its legitimacy.
7.2 Putting API security at the core
Perform comprehensive discovery, categorization and monitoring of all APIs. Implement strict API access control policies and deploy protective measures that can detect and block abuse attacks against API business logic. Specific measures include:
-API Discovery & Inventory: Build a complete inventory of API assets, including internal, external, and third-party APIs.
-API Gateway and Authentication: Use an API gateway to centrally manage API access and implement strong authentication (e.g. OAuth 2.0, JWT) and authorization mechanisms.
-Rate limiting and quota management: Implement rate limiting and quota management for API calls to prevent abuse and DDoS attacks.
-Input validation and data cleansing: Strict validation and cleansing of all API inputs to prevent injection attacks and data leakage.
-Business Logic Protection: Deploy a security solution that understands and protects API business logic, detecting and blocking abusive attacks against specific business processes.
-API monitoring and logging: continuously monitor API traffic and record all API calls for after-action analysis and forensics.
7.3 Enhanced account security against the ATO
Employ multi-factor authentication (MFA), but more importantly, deploy advanced solutions capable of detecting anomalous login behavior, device fingerprint anomalies, and credential stuffing attacks. Specific measures include:
-Mandatory MFA: Mandatory multi-factor authentication for all user accounts, especially for high-value accounts and sensitive operations.
-Device Fingerprinting: Tracks and analyzes the unique characteristics of a user's device, identifying login attempts from new or suspicious devices.
-Behavioral biometrics: Monitor users' behavioral patterns, such as typing speed, mouse movements, and navigation habits, to identify abnormal behavior.
-Credential padding detection: Deploy specialized solutions to detect and block credential padding attacks, such as monitoring for large numbers of failed login attempts or logins from known malicious IPs.
-Password policy and leakage detection: Enforce strong password policies and regularly check user passwords for known data leaks.
-Account lockout and alerts: Implement an account lockout mechanism for multiple failed login attempts and send alert notifications to the user.
7.4 Establishment of a unified security view
Integrate the security protection of Web, API and mobile applications into a unified platform to achieve unified management of policies andThreat intelligenceof sharing to address complex attacks across channels. A unified security platform should be able to:
-Centralized management: Provides a single console to manage all security policies and configurations.
-Threat Intelligence Sharing: Share threat intelligence between different security components to improve overall defense capabilities.
-Cross-channel visibility: Provides full visibility into all traffic (Web, API, mobile) to identify cross-channel attack patterns.
-Automated response: Enables automated threat response and mitigation measures, reducing manual intervention and response time.
7.5 Continuous Monitoring and Threat Intelligence
Security is an ongoing process, not a one-time deployment. Businesses need to:
-Real-time monitoring: Continuously monitor all traffic and user activity to detect and respond to threats in a timely manner.
-Threat Intelligence Subscription: Subscribe to threat intelligence services to stay up-to-date on the latest attack trends and techniques.
-Periodic security assessments: Conduct regular security assessments and penetration tests to identify and fix potential vulnerabilities.
-Security Awareness Training: Provide security awareness training to employees to improve their ability to recognize and respond tocyber threatsThe ability of the
8. Conclusion
The Imperva 2025 Malicious Bots Report paints a picture of a future cyber threat dominated by AI and automation. In this new normal, malicious bots are no longer simple scripts or tools, but intelligent adversaries capable of learning, adapting and evading. The milestone change of automated traffic exceeding human traffic for the first time signals that we are entering a new era of cybersecurity.
The three core trends revealed in the report - the dominance of automated traffic, the evolution of AI-enabled attacks, and the emergence of APIs as the new battleground - collectively constitute the fundamental features of the current threat landscape. These trends not only change the scale and complexity of attacks, but also pose fundamental challenges to traditional security defenses.
Enterprises must abandon passive and static defense thinking and actively adopt a new generation of data- and intelligence-drivenApplication securityArchitecture. This includes deploying advanced bot protection solutions, hardening API security, countering account takeover attacks, and creating a unified view of security. Only through a multi-layered, adaptive defense-in-depth system can enterprises protect their digital assets and business continuity in this ongoing confrontation between man and machine.
In the face of the increasingly intelligent and scaled threat of malicious bots, security is no longer an option, but a foundation for business survival and growth. Enterprises need to integrate security into every aspect of digital transformation, consider security factors from the design stage (Security by Design), and continuously monitor and optimize security measures. Only in this way can they ensure the security, stability and sustainability of their business in this new automation-driven era.
Original article by Chief Security Officer, if reproduced, please credit https://www.cncso.com/en/2025-ai-powered-attacks-and-api-security.html