Chief Security Officer (CSO) is a complex and multifaceted position whose main responsibilities include information security, enterprise security operation status, or both. The CSO's role and responsibilities may vary from company to company. Some CSOs may be responsible for protecting physical security, such as the security of company data center equipment; others may focus on digital information security, such as preventing company networks from being hacked.
Chapter 1 Definition of Chief Security Officer
Chief Security Officer (CSO) is the highest person in charge of the organization's overall security strategy, policy and execution in the senior management. In the modern enterprise governance structure, the CSO's function has evolved from the traditional physical asset protection to a cross-cutting integrated management role, covering physical security, information security, personnel security and supply chain security and other dimensions.
From an academic perspective, the role of the CSO embodies an organization's ability to mitigate risk in an environment of uncertainty. Unlike traditional security executives, CSOs need to balance security investments with business efficiency while safeguarding the core assets of the organization from being compromised.
|
dimension (math.) |
Head of Traditional Security |
Chief Security Officer (CSO) |
|
Scope of responsibilities |
Focus on specific areas (e.g. surveillance, access control) |
Global security governance (physical + digital + psychological) |
|
Reporting to |
Administrative Manager or IT Manager |
Chief Executive Officer (CEO) or Board of Directors |
|
Core competencies |
Focus on technology or implementation |
Focus on strategic decision-making, business insight and risk balancing |
|
goal-oriented |
Reduction of security incidents |
Ensure Business Continuity and Enhance Enterprise Resilience |
It is worth noting that there is a significant difference between the functions of the CISO and the CISO, as the CISO usually focuses on the protection of digital assets, network infrastructure and data privacy, which is an in-depth extension of the information technology field, while the CSO's vision is more macroscopic, focusing not only on the defense of the “bit” world, but also on the physical security of the “atom” world and the overall risk resilience of the enterprise at the legal, compliance and reputational levels. The CSO's vision is more macro, focusing not only on the defense of the "bit" world, but also on the physical security of the "atom" world, as well as the enterprise's overall anti-risk capability at the legal, compliance and reputation levels. In some large multinational enterprises, CSOs often act as superiors or equals of CISOs to jointly build a comprehensive security defense system for the enterprise.
Chapter II Responsibilities of the Chief Security Officer
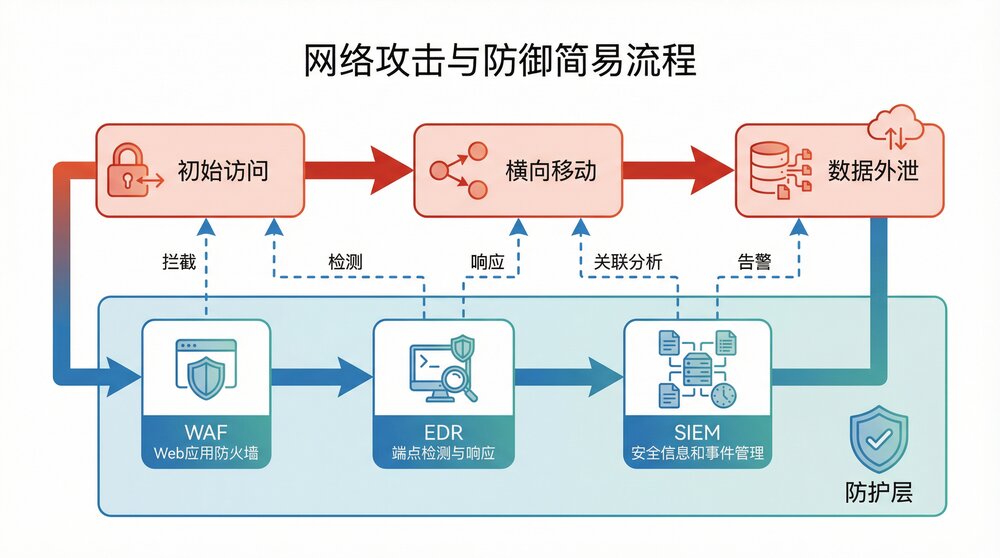
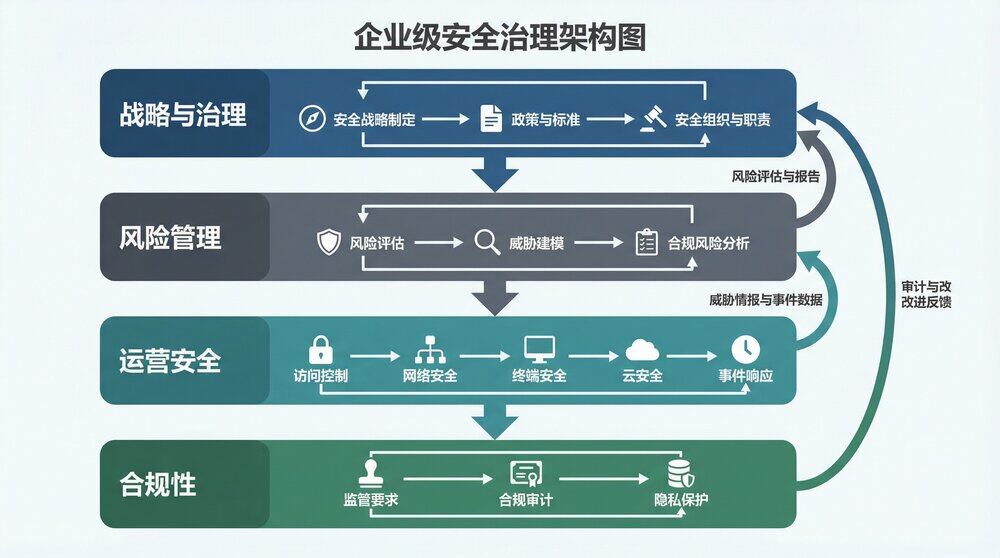
The Chief Security Officer's system of responsibilities is built on the core cycle of defense, detection, response, and recovery. Its core mission is to ensure that the organization's assets, people, and reputation remain stable in a complex and changing external environment. Specifically, the CSO's responsibilities can be broken down into the following four core dimensions:
-
Strategic planning and governance
The CSO is responsible for developing and maintaining an enterprise-level security vision and strategic framework. This requires the CSO to have a deep understanding of the organization's business model and to translate security objectives into measurable business metrics. By benchmarking against international standards (e.g., ISO 27001 or NIST CSF), the CSO needs to establish a comprehensive set of policies to ensure that security efforts are well documented and followed within the organization.
-
Risk management and decision-making
Risk management is the soul of the CSO's work, who needs to identify and evaluate all kinds of risks that may affect the business objectives, including but not limited to cyber-attacks, physical penetration, natural disasters and internal fraud. Under the premise of limited resources, CSOs must decide on risk avoidance, reduction, transfer or acceptance through scientific quantitative risk analysis, so as to realize the optimal ratio of security cost and business benefit.
-
Compliance and Legal Affairs
As global data protection laws (e.g., GDPR, People's Republic of China Data Security Law) become increasingly stringent, CSOs are tasked with ensuring that their organizations operate in a legally compliant manner. This includes managing the security risks of third-party vendors, coordinating internal audits, and responding to regulatory agency inspections to avoid exposing the organization to hefty fines or lawsuits.
-
Emergency response and business continuity
In the event of a crisis, the CSO is the “war commander” of the organization. With responsibilities that include the establishment of a highly effective CERT, a detailed Business Continuity Plan (BCP) and a Disaster Recovery Plan (DRP), the CSO must ensure that, in the event of an extreme shock, the organization is able to quickly restore core functions and minimize losses.
|
Category of responsibility |
Core outputs |
labor value (in economics, the labor inherent in a commodity) |
|
Strategic governance |
Security white papers, annual planning |
Establishing organizational security direction |
|
risk control |
Risk inventory, assessment reports |
Reduction of uncertainty losses |
|
Compliance audit |
Compliance reports, audit vouchers |
Reducing legal and regulatory risk |
|
emergency protection |
Response plans, exercise records |
Enhance tissue resilience |
Chapter 3 Positioning, Role, and Role of the Chief Security Officer at the Enterprise Level
In the modern enterprise organizational structure, the positioning of the Chief Security Officer has been transformed from a traditional “cost center” supporter to a “value center” enabler. This evolution in positioning and role reflects the increased strategic importance of security in business competition.
-
Positioning of the corporate hierarchy
The CSO is typically at the CXO level and ideally reports to the Chief Executive Officer (CEO) or the Risk Management Committee of the Board of Directors. This high-level positioning ensures that security decision-making cuts right through business unit resistance and receives the necessary resource support and executive authorization. In academic modeling, this positioning is referred to as the “top level of security governance” and is designed to address the information asymmetry between security and the business.
-
Multiple Role Analysis
Strategic decision makers: CSOs are not just technical gatekeepers, but also participants in business strategy. CSOs provide decision support from a security perspective to prevent potential “security traps” when a company undertakes a merger or acquisition, enters a new market, or launches a new product.
Cross-departmental coordinator: Security is an activity that runs through the entire life cycle of an organization, and CSOs need to break down the barriers between HR, legal, IT, production and other departments to build a collaborative and linked security landscape.
Guardian of corporate reputation: In a data-driven era where security incidents are often accompanied by reputational crises, CSO enhances the trust of customers, investors, and regulators by establishing transparent security mechanisms.
-
Central role played
The core role of the CSO is reflected in“Empowerment”together with“Guarantee.”The balance. First, by building underlying security resilience, CSO provides a testing ground for business innovation, so that enterprises dare to try high-risk, high-reward digital transformation; second, in the face of globalized competition, CSO helps enterprises to meet the challenges of transnational compliance, and becomes the escort for their international expansion.
Expert Opinion:
The highest level of CSO is to internalize safety into the cultural DNA of the enterprise. When every employee becomes a part of the safety defense line, the role played by CSO will change from “control” to “leadership”.
Chapter 4: Chief Security Officer Growth Experience and Process
The professional growth of the Chief Security Officer is a long-term process of transformation from a “technical specialist” to a “complex manager”. This path usually follows the logic of evolution from point to point, from technique to way, and can be summarized in the following four key stages:
-
Technology accumulation period: depth determines height
Early in their careers, successful CSOs usually have a strong background in one of the technical areas of security (e.g., code security, network attack and defense, cryptography, or system architecture). The core objective at this stage is to understand the underlying logic of security and to master the “attacker's perspective”. Only through the baptism of the actual combat confrontation, the future in the development of strategy can avoid the paper.
-
Period of field expansion: width determines breadth
As experience increases, prospective CSOs begin to step outside of a single technical area and focus on the integrity of the security system. This includes learning about physical security management, privacy protocols, legal compliance guidelines, and project management methodologies. At this point, the practitioner begins to move from “solving a vulnerability” to “building a defense system,” initially adopting the mindset of an architect.
-
Managing transitions: dimensions determine strength
After moving into a management position, the focus shifts to people management and resource scheduling.CSOs need to learn how to communicate with executives from non-technical backgrounds, how to prepare and manage multi-million dollar security budgets, and how to deal with the complexities of workplace politics and benefit gaming. The mark of success at this stage is the ability to translate the language of security into the language of business and gain the understanding and cooperation of the business units.
-
Strategic upliftment: the pattern determines the outcome
The key to becoming a CSO is the fusion of leadership and business insight. At this stage, security is no longer a purely technical endeavor, but part of corporate governance, and CSOs need to possess macro-political and economic acumen, be able to anticipate industry trends, and demonstrate calm decision-making and strong psychological qualities in times of crisis.
|
point |
Core Keywords |
Key challenges |
|
Technological Precipitation Period |
Attack and defense, code, tools |
Rapid changes in technology |
|
Field Expansion Period |
Architecture, Compliance, Processes |
Fragmentation of knowledge systems |
|
Managing the transition period |
Budget, team, communication |
Conversion of language systems |
|
period of strategic upgrading |
Business, decision-making, culture |
Balancing complex interests |
Chapter 5 How to Become a Chief Security Officer: Path Planning
For security practitioners aspiring to become a Chief Security Officer (CSO), career planning should be a long-term and systematic project. The top of the security industry pyramid requires not only technical geniuses, but also leaders with business acumen. Below is a 10-year growth path for graduates:
-
Start-up phase (0-3 years): building a technology moat
Graduates should focus on honing their practical skills for the first three years of employment. It is recommended to choose a large enterprise with a well-established security team or a professional security service organization as a starting point.
Learning focus: network protocols, operating system principles, mainstream attack and defense techniques.
Key Actions: Participate in front-line penetration testing or security operations work, get basic certifications (e.g., Security+ or CISSP-Associate).
Mindset building: maintain sensitivity to new technologies (e.g., AI security, intelligent body vulnerabilities) and establish a habit of continuous learning.
-
Growth phase (3-7 years): making the leap from technology to architecture
After acquiring solid skills, you should proactively seek opportunities to work on complex projects, such as building enterprise security systems or large-scale data compliance programs.
Learning Focus: Security Architecture Design (Zero Trust, SDL), Risk Assessment Methodology, Laws and Regulations (Equalization 2.0, GDPR).
Key Actions: Try to take the lead in full lifecycle management of a medium-sized project, get advanced certifications (e.g. CISSP, CISA).
Mindset building: Start trying to think about security from a business perspective, thinking about “how security can create value for the business”.
-
Leapfrog phase (7-12 years): developing managerial and strategic thinking
The goal at this stage is to move into the middle and upper management sequence.
Focus of study: financial and budgetary management, human resources management, public relations and crisis management.
Key Actions: Pursue an MBA or related management degree, actively participate in industry summits, and build personal industry influence.
Mindset building: learn to give up excessive obsession with technical details and focus on the improvement of organizational capabilities and the achievement of strategic goals.
-
Topping out phase (12 years +): taking charge of security
At this point, the practitioner has all the qualities to become a CSO.
Core competencies: ability to talk to the board, quantify security risks as financial risks, and make the right decisions under extreme pressure.
Suggested Path: Look for organizations that are in a period of rapid expansion or facing significant compliance pressures, where the need for a strategic CSO is often more acute.
|
phase |
Recommended positions |
Core Skills Package |
Certificate of Recommendation |
|
1-3 years |
safety engineer |
Attack and defense practice, script development |
Security+, CEH |
|
3-7 years |
Security Architect/Specialist |
Architecture design, risk management |
CISSP, CISA |
|
7-12 years |
safety director |
Team leadership, budget management |
CISM, MBA |
|
12 years + |
Chief Security Officer (CSO) |
Business decision-making, macro-governance |
CCISO |
Chapter VI. References
Reference to authoritative standards, laws and regulations and industry research results in the field of security governance at home and abroad, mainly including:
International standards and frameworks:
International Organization for Standardization. (2022). ISO/IEC 27001: Information security, cybersecurity and privacy protection - Information security management systems - Requirements. Requirements.
National Institute of Standards and Technology. (2024). The NIST Cybersecurity Framework (CSF) 2.0.
Laws and regulations:
Standing Committee of the National People's Congress of the People's Republic of China. (2021). Data Security Law of the People's Republic of China .
European Union. (2016). General Data Protection Regulation (GDPR).
Industry Guides and Reports:
OWASP Foundation. (2020). CISO MindMap and Application Security Guide.
Gartner. (2023). Leadership Vision for 2024: Chief Information Security Officers.
(ISC)². (2023). Cybersecurity Workforce Study: Looking for the Leaders of Tomorrow.
Academic and Professional Literature:
Chen, She-Ying. (2009). Innovative Thinking in NGO and Policy Research. South China Today.
A series of in-depth interviews and technical columns with industry experts on the evolution of the CSO and CISO functions.